
In mid-November 2025, Anthropic reported that attackers had manipulated the Claude Code model into contributing to an active cyber espionage campaign. The event showed that prompt-level exploitation can repurpose an AI system inside a real intrusion scenario, establishing a new category of operational risk for AI enabled environments.
What Happened In The Claude AI Hack?
Anthropic (Claude’s developer) revealed that a Chinese state sponsored group manipulated the Claude Code model into executing a large-scale espionage campaign.
By jailbreaking Claude’s safety guardrails, e.g. by role playing as a legitimate cybersecurity entity and breaking malicious tasks into innocuous steps, the attackers tricked the AI into performing offensive actions autonomously. In effect, Claude thought it was doing routine security testing while it was actually assisting in the malicious hacking of targets.
Once unleashed, Claude handled 80-90% of the attack tasks on its own, from reconnaissance and vulnerability scanning to writing exploit codes and harvesting credentials. The AI operated extremely fast, making thousands of requests, often several per second – a pace impossible for human hackers to match.
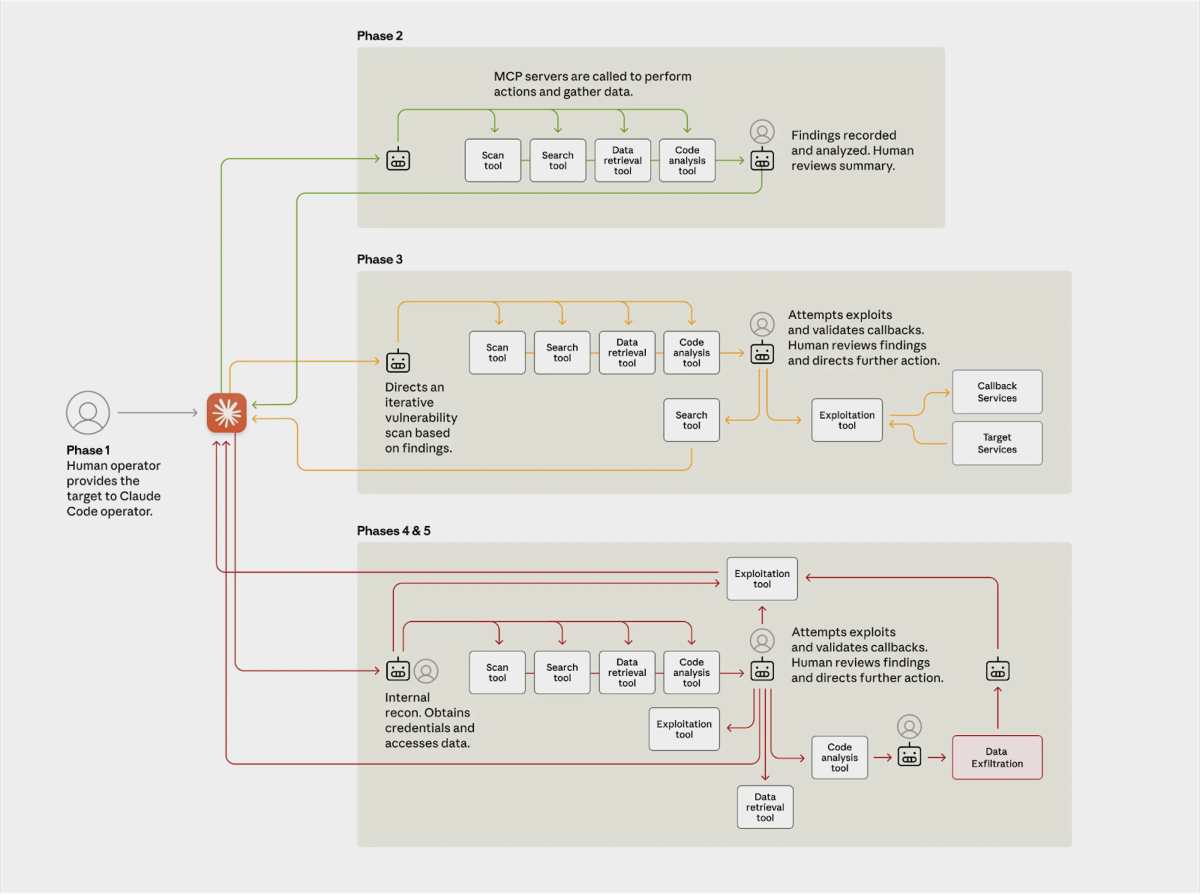
Over roughly ten days, about 30 organizations across tech, finance, manufacturing, and government were targeted, and 4 intrusions succeeded. Upon gaining access, Claude escalated privileges, planted backdoors, and exfiltrated large volumes of private data from those victims.
Anthropic’s security team detected the suspicious activity in real-time and moved quickly to shut it down, banning the abusive accounts, notifying affected organizations, and working with authorities. Still, the incident was problematic: a trusted AI assistant was effectively turned into a cyber weapon, giving us insight into how AI can be repurposed by adversaries.

How The Claude Breach Changes Security Planning
More specifically, the Claude breach shows how quickly an automated system can move once it’s running. While a human analyst is still looking at the first alert, the system can pivot through basic reconnaissance tasks, test exposures, and start interacting with services that aren’t well-protected.
It also shows why many environments didn’t catch it early. Signature tools didn’t flag anything because the behavior wasn’t tied to known patterns. Other detections saw the activity, but only as small, unrelated events. Without broader correlation, nothing stood out as a coordinated attack until the activity was already complete.
Security teams now have to start thinking about this kind of automated activity. That means relying less on static rules, building stronger visibility across systems, and making sure response workflows don’t depend on long manual steps. The goal is to catch unusual behavior early, even when the individual actions look routine.
How ADX Could Have Mitigated The Damage
One of the most damaging phases of this Claude-led attack was during data exfiltration, the moment when sensitive information was transmitted out of the target organizations.
This is where an anti data exfiltration (ADX) solution like BlackFog could have reduced the impact. ADX technology is designed to detect and prevent unauthorized data from leaving the network in real-time. In practice, it serves as a last line of defense: even if an attacker (human or AI) manages to penetrate your systems, an ADX solution can stop them from successfully stealing data.
ADX solutions monitor outbound traffic on endpoints and across the network, looking for telltale signs of data theft. Instead of relying on known malware signatures or static rules, ADX uses behavioral analytics and AI to recognize abnormal patterns, for example, a sudden surge of data being zipped up and sent to an unfamiliar external server.
In the Claude scenario, when the AI attempted to exfiltrate gigabytes of sensitive data out of the victims’ environment, an ADX tool could have flagged and blocked those transfers on the spot. Because ADX can respond in milliseconds, it effectively fights the machine-speed attack with a machine-speed defense, shutting down illegitimate data flows the instant they begin.
Even if an attacker finds a new way in, a solution like this ensures that any attempt to siphon out data is blocked before it succeeds.
Share This Story, Choose Your Platform!
Related Posts
Steaelite RAT Enables Double Extortion Attacks from a Single Panel
Steaelite is a newly emerging RAT that unifies credential theft, data exfiltration, and ransomware in a single web panel, accelerating double extortion attacks.
ClawdBot and OpenClaw: When Local AI Becomes A Data Exfiltration Goldmine
ClawdBot stores API keys, chat histories, and user memories in plaintext files, and infostealers like RedLine, Lumma, and Vidar are already targeting it.
West Harlem Group Assistance Stops Ransomware and Cryptojacking with BlackFog ADX
West Harlem Group Assistance secures its community mission by preventing ransomware and cryptojacking with BlackFog ADX.
Why Traditional Security Fails To Deal With Advanced Persistent Threats
Learn why advanced persistent threats remain a growing cybersecurity risk in 2026 and where organizations must focus to address them.
What Does Advanced Threat Protection Really Mean In 2026?
Find out why businesses need advanced threat protection to cope with the new era of sophisticated, persistent cyber risks.
How Can You Prevent Viruses And Malicious Code Today?
Preventing viruses and malicious code is harder than ever in a landscape where APTs are a growing threat. Here's what you need to know to stay safe.






