Stop Data Exfiltration. Stop Cyberattacks.
Hackers don’t win when they break in, they win when they get data out. That’s why data exfiltration is the true endgame of every cyberattack.
BlackFog’s anti data exfiltration (ADX) technology blocks unauthorized transfers in real-time, ensuring your sensitive information never leaves your devices or network.
When the data stays inside, breaches fail, ransoms collapse, and your organization stays resilient.

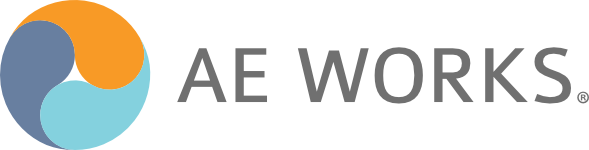
ADX Protect consists of endpoint agents and the BlackFog console. The BlackFog console allows you to manage groups of devices and provides a centralized view of all threats and events generated at the endpoint.
- Works seamlessly alongside existing endpoint security and AntiVirus solutions.
- Centralized management console
- Managed Service Provider Ready
- Integrates with Ticketing solutions
- Available with different tiers of data retention


On-Device Data Privacy
BlackFog’s data privacy features decrease the risks associated with data loss and data breaches.
- Mitigate the risk of data loss through geofencing
- Minimize data collection on every endpoint
- Prevent unauthorized data collection and profiling
- Anonymize user behavior
- Secure all device data with on-device protection
- Protect your remote workers wherever they are
On-Device Data Security
Data security is now one of the biggest issues in cybersecurity. Increasing regulations, compliance and accountability pose significant risk to all organizations globally. ADX Protect helps organizations manage the risk by:
- Preventing data loss using AI and ML based algorithms
- Reducing the surface attack area exposed to attackers
- Detailed reporting and analysis of threat vectors
- Lowering the cost of compliance
- Detecting network anomalies through data exfiltration
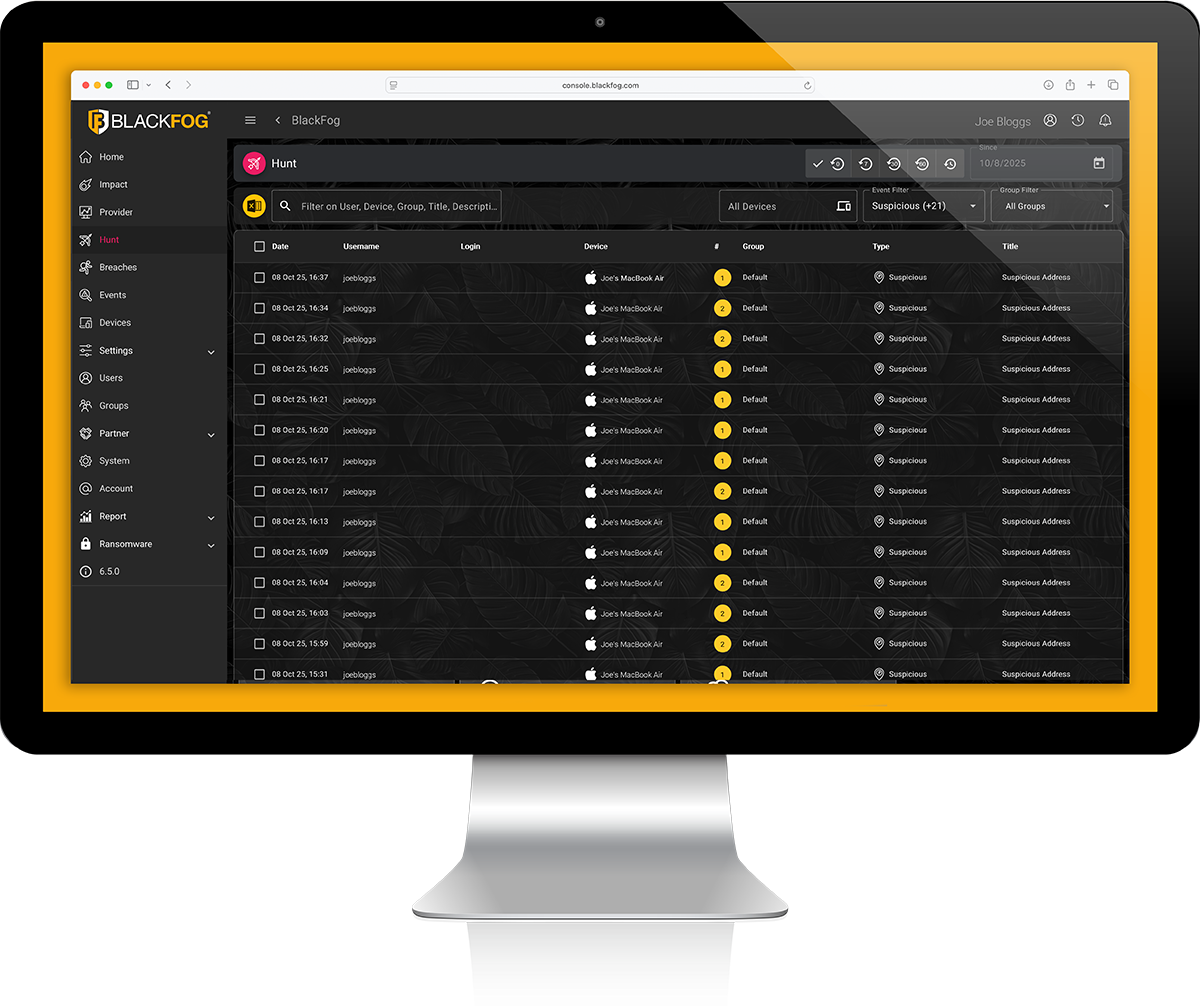
Insider Threat Prevention
Insider threats represent one of the largest growing groups of threats within an organization, from employees stealing corporate secrets to industrial espionage and the use of AI. BlackFog mitigates these risks by:
- Protecting endpoint devices from millions of threats
- Mitigating Advanced Persistent Threats (APT) on the network
- Controlling the exfiltration of data outside the network
- Protection from threats and activation over the Dark Web
- Eliminating Fileless Network execution attack vectors
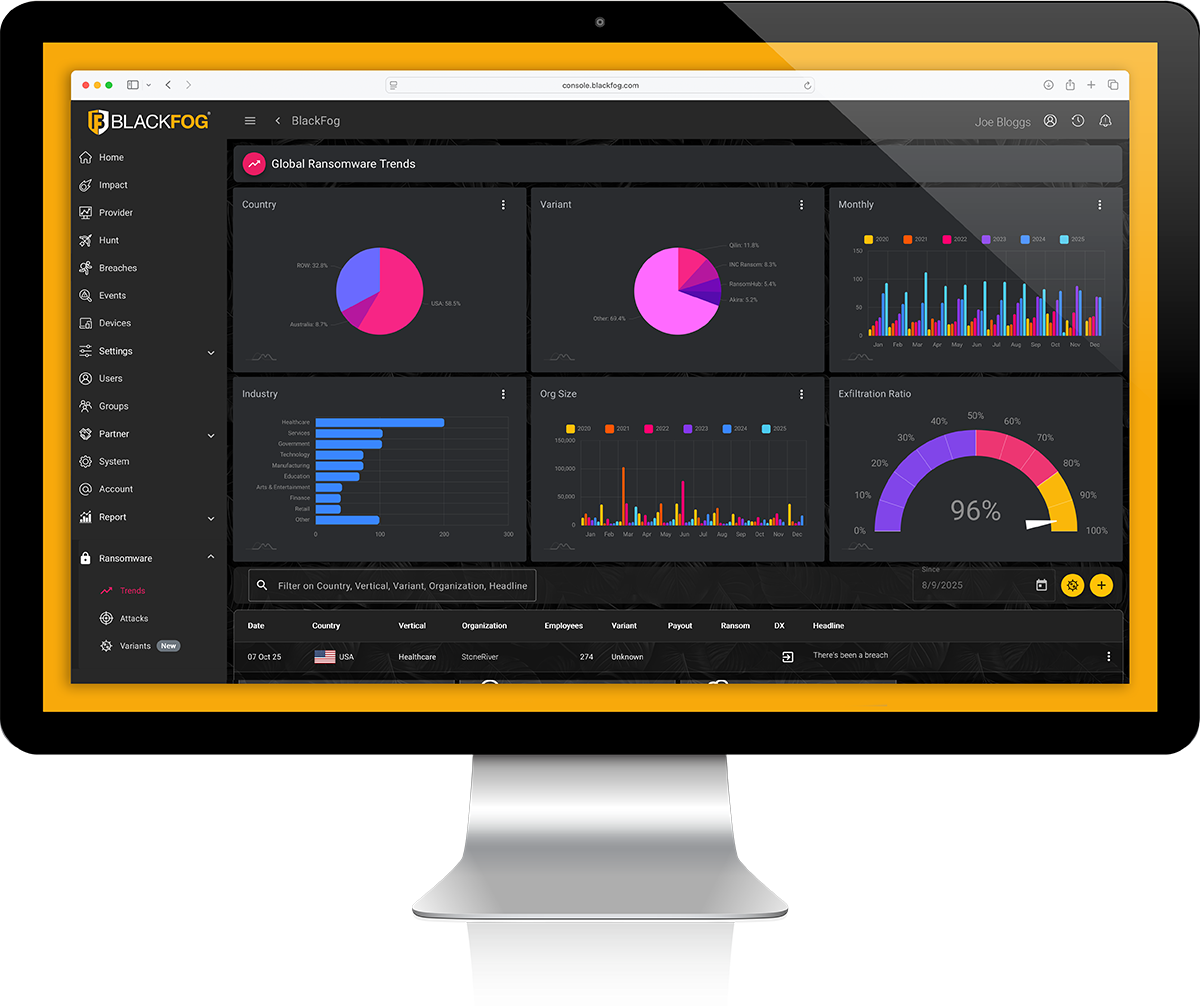
Real-Time Analytics
- Detailed analytics provide impact assessment on threats across your entire organization
- Provide insight into exfiltration by protocol, country and domain
- Export event and device data directly into Microsoft Excel
- Post event analysis using built-in search engine
- Automatic grouping of events for analysis