
Cybersecurity Compliance: What You Need Without Hiring A CISO
Cyberthreats are no longer a concern reserved for large enterprises. Small and mid-sized businesses are increasingly targeted by ransomware groups and data theft campaigns, often because attackers assume the defenses and governance structures in place in these organizations are less mature. But while most companies know what’s required of them as regulatory requirements tighten and customer expectations rise, putting these principles into practice is often where hurdles lie.
Indeed, what many growing firms struggle with is not awareness, but capability. Cybersecurity compliance requires strategy, oversight and continuous monitoring. Yet hiring a full-time Chief Information Security Officer (CISO) to oversee this is often beyond the budget of smaller organizations. The challenge is therefore finding a way to meet compliance obligations, protect sensitive data and reduce risk without building an expensive executive security function.
What Is Cybersecurity Compliance?
Cybersecurity compliance refers to the ongoing process of ensuring that an organization’s technology, policies and security controls meet established standards designed to protect sensitive data from unauthorized access and theft. In practical terms, it means demonstrating that reasonable safeguards are in place to reduce cyber risk and prevent incidents such as ransomware attacks and data exfiltration.
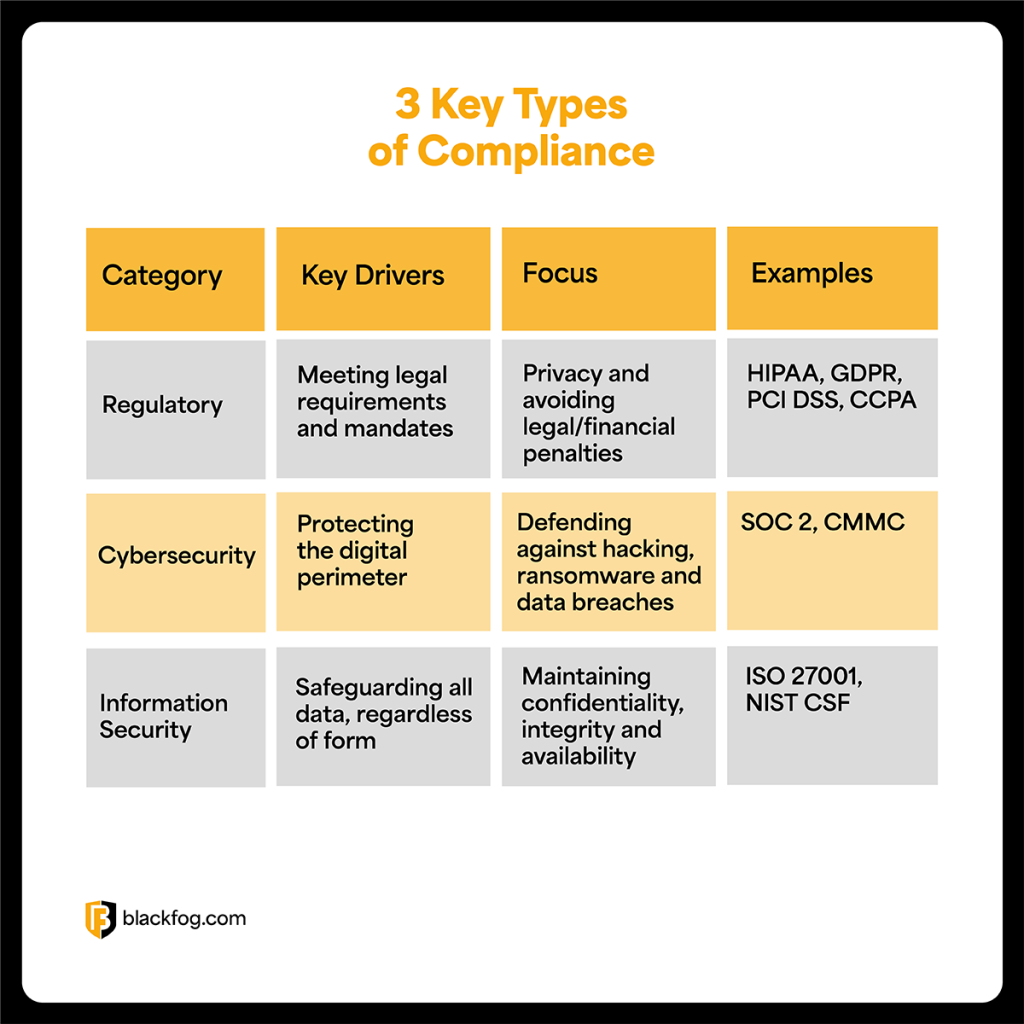
There are several related concepts within compliance that it’s important to be aware of. Regulatory compliance, for example, focuses on meeting specific legal requirements such as HIPAA, PCI DSS or state privacy laws. Meanwhile, information security compliance centers on aligning internal security practices with recognized frameworks like NIST or ISO 27001.
Cybersecurity compliance brings these elements together by combining legal obligations, technical controls and governance oversight into a coordinated approach to risk management. While these areas overlap in areas such as access control, encryption and monitoring, cybersecurity compliance is broader in scope. It requires continuous risk assessments, documented policies, employee training and active monitoring of threats.
Compliance is not achieved once and forgotten. It must be treated as an ongoing process that adapts as threats, technologies and business operations evolve.
“Cybercriminals don’t differentiate between enterprise and mid-market. They target opportunity. For many growing organizations, the challenge isn’t understanding the risks, it’s having the leadership and oversight to manage it. That’s where a vCISO model becomes transformative, delivering executive-level security strategy without the executive-level overhead.”
– Darren Williams, CEO and Founder, BlackFog
Why Cybersecurity Compliance Matters More Than Ever
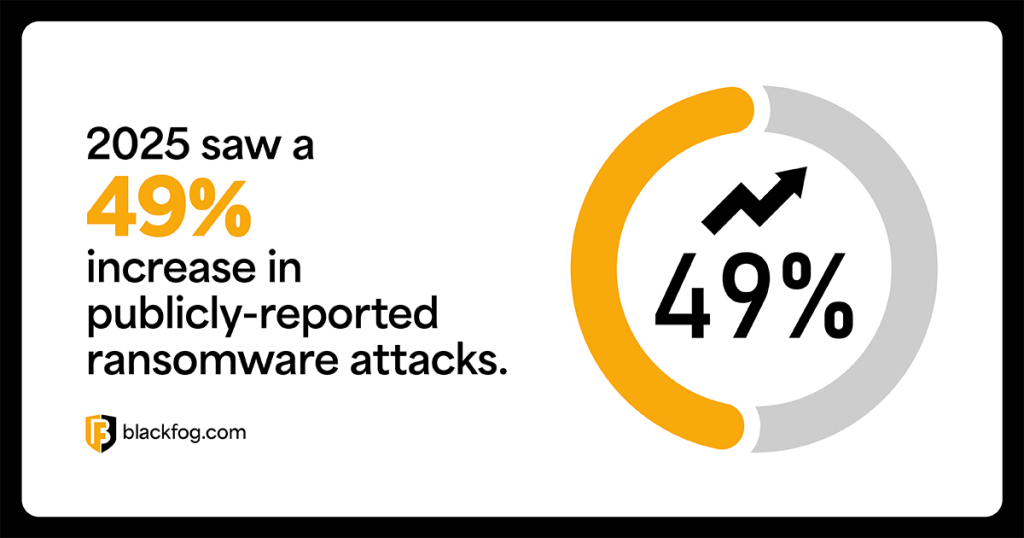
Cyberthreats are accelerating in scale and intent. BlackFog’s latest State of Ransomware Report found that publicly disclosed ransomware attacks rose 49 percent year-on-year in 2025, reaching a record 1,174 incidents. However, the research also indicates that ransomware activity is far more extensive than public reporting suggests, with our estimates suggesting 86 percent of attacks go undisclosed.
This trend matters for compliance because modern ransomware is increasingly tied to data theft and extortion. When sensitive information is exfiltrated, the incident becomes more than downtime. It creates breach notification duties, potential regulatory exposure and lasting damage to customer trust.
Regulators are tightening expectations as the threat landscape worsens, but pressure is also commercial. Third-party and supply chain risks are some of the most common causes of data breaches, so enterprise procurement teams and risk committees increasingly require suppliers to demonstrate alignment with security frameworks. This means small firms are increasingly expected to provide evidence of active controls and undergo third party assessments before contracts are awarded or renewed.
The Cost Of Non-Compliance
Failing to maintain cybersecurity compliance carries consequences that extend far beyond a single incident. For many organizations, especially small and mid-sized firms, the impact can threaten long-term stability.
- Financial penalties: Regulators can impose significant fines for failing to protect sensitive data or meet reporting obligations, with penalties that often scale based on revenue or severity of negligence.
- Lawsuits and legal exposure: Data breaches often trigger class action claims, shareholder actions and contractual disputes, leading to prolonged litigation and costly settlements.
- Brand damage: Loss of customer trust can result in long-term reputational harm, reduced market confidence and sustained revenue decline.
- Loss of contracts: Enterprise clients increasingly require documented compliance with recognized security frameworks. Failure to demonstrate adequate controls can lead to lost bids or terminated agreements.
- Cyber insurance denial: Insurers are tightening underwriting standards and organizations without documented compliance and risk management controls may face denied claims, higher premiums or reduced coverage after an incident.
Collectively, these consequences can jeopardize a company’s future. Smaller enterprises often lack the financial reserves, legal resources and operational resilience required to absorb these shocks, making proactive compliance essential for survival.
Understanding Cybersecurity Compliance Standards In The US
Businesses operating in the US face a complex landscape of cybersecurity compliance standards and legal requirements. The specific obligations that apply depend on industry, the type of data handled and whether the organization works with government agencies or large enterprises. Below are several of the most commonly encountered frameworks and regulations all firms must be mindful of.
HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) is a legal mandate that applies to healthcare providers, insurers and any associated organization that handles protected health information. HIPAA requires administrative, technical and physical safeguards to protect patient data, along with breach notification procedures and ongoing risk assessments. Non-compliance can result in significant federal penalties and corrective action plans.
PCI-DSS
The Payment Card Industry Data Security Standard (PCI-DSS) is an industry standard applying to any business that stores, processes or transmits credit card information. It requires strict access controls, encryption, network security measures and regular vulnerability testing. Compliance is enforced by payment brands and acquiring banks, and failure to comply can result in fines, increased transaction fees or loss of card processing privileges.
SOC 2
System and Organization Controls (SOC) 2 is a voluntary but widely expected compliance framework for service organizations, particularly technology and SaaS providers. It evaluates controls related to security, availability, processing integrity, confidentiality and privacy. Organizations must undergo independent third-party audits to demonstrate compliance, which is often required to secure enterprise contracts.
NIST
The National Institute of Standards and Technology (NIST) Cybersecurity Framework provides guidance on identifying, protecting, detecting, responding to and recovering from cyberthreats, as well as governance. While not a law for most private companies, it is widely adopted as a best practice standard and frequently required in federal contracts and enterprise vendor assessments.
CMMC
The Cybersecurity Maturity Model Certification applies to contractors within the US Department of Defense supply chain. It establishes graduated security requirements based on the sensitivity of information handled. While basic requirements allow for annual self-assessments, higher levels involving sensitive data require formal third-party or government audits to achieve certification. Failure to meet required levels can prevent participation in defense contracts.
Do You Really Need A Full-Time CISO?
Appointing a skilled and experienced CISO is often viewed as the gold standard for ensuring cybersecurity leadership and regulatory compliance. In large enterprises, a dedicated executive can provide strategic oversight, coordinate security programs and maintain alignment with evolving regulatory requirements.
However, this is an enterprise-level solution. For many small and mid-sized businesses, hiring a full-time CISO may not be practical or financially sustainable. Challenges for these companies include:
- High salary and benefits: Experienced CISOs command substantial compensation packages, often including six-figure salaries, bonuses and long-term incentives that may exceed the security budget of smaller firms.
- Skills shortages: There is a well-documented shortage of qualified cybersecurity leaders, making experienced candidates both scarce and highly in demand.
- Recruitment challenges: Identifying, vetting and retaining the right executive talent requires time, resources and internal expertise that many growing organizations lack.
For businesses that require strategic security leadership but cannot justify a permanent executive hire, alternative models are emerging. One increasingly common approach is the virtual CISO, or vCISO, which provides experienced cybersecurity oversight on a flexible and cost-effective basis.
The Virtual CISO Model: A Smarter Path To Cybersecurity Compliance
For organizations that need executive-level cybersecurity leadership but cannot justify a full-time hire, the vCISO model offers a practical alternative. It works with leadership teams to build and maintain a structured cybersecurity framework that aligns with regulatory requirements and recognized standards. This typically includes conducting formal risk assessments, identifying control gaps and prioritizing remediation efforts.
A vCISO can support audit preparation by ensuring documentation is complete and controls are defensible. They also assist with policy creation, incident response planning and ongoing board reporting to demonstrate accountability and measurable progress.
For smaller enterprises, this model delivers access to senior expertise while preserving budget flexibility, as well as offering access to advanced technology. BlackFog’s ADX Instinct, for example, strengthens this approach by providing advanced anti data exfiltration capabilities that support compliance objectives.
By preventing unauthorized data transfers and delivering visibility into endpoint activity, ADX Instinct helps organizations demonstrate active controls and continuous monitoring, both of which are critical components of modern cybersecurity compliance.
Step-by-Step: Achieving Compliance Without Hiring A CISO

Organizations do not need a full-time CISO to build a structured and defensible compliance program. What they do need is a disciplined approach, clear accountability and access to experienced guidance. A vCISO model supports each of the following critical steps.
- Risk assessment: Conduct a formal evaluation of assets, data flows and threat exposure to understand where sensitive information resides and how it is accessed. A vCISO structures this process, prioritizes risks and aligns findings with applicable standards.
- Gap analysis: Compare existing controls against required frameworks such as NIST, HIPAA or PCI-DSS to identify weaknesses in safeguards, policies or documentation. A vCISO translates these gaps into a clear remediation roadmap.
- Policy framework: Develop documented policies covering access control, data handling, remote work and incident response. A vCISO ensures policies are practical, enforceable and aligned with regulatory expectations.
- Technical controls: Implement safeguards such as endpoint protection, encryption and anti data exfiltration technology. Solutions like BlackFog’s ADX Instinct help prevent unauthorized data transfers and support ongoing compliance.
- Monitoring and reporting: Establish continuous monitoring and structured reporting to leadership. A vCISO helps by defining measurable indicators that demonstrate control effectiveness and accountability.
- Incident response planning: Create and test a documented response plan that defines roles, communication procedures and regulatory notification requirements to ensure readiness if an incident occurs.
Compliance Is Leadership, Not Just Documentation
Cybersecurity compliance cannot be delegated solely to IT teams or treated as a documentation exercise completed once a year. It requires visible leadership, executive accountability and a commitment to ongoing risk management. No matter the size of an organization, this must be driven from the top, with clear ownership of policies, controls and oversight.
For firms that cannot justify the cost of a full-time CISO to take control of these activities, managed services such as a vCISO provide access to experienced guidance without the financial burden of a permanent executive hire. This approach helps reduce risk, strengthen governance and demonstrate measurable progress to regulators, partners and customers.
In competitive markets, particularly for smaller providers serving larger enterprises, the ability to show structured compliance and active security oversight can become a differentiator. It signals maturity, builds trust and reassures stakeholders that cybersecurity risk is being managed with intent and discipline.
Frequently Asked Questions About Cybersecurity Compliance
How can cyber range platforms support cybersecurity compliance?
Cyber range platforms simulate real-world attack scenarios, allowing organizations to test controls, validate incident response plans and demonstrate preparedness in secure, isolated environments. This helps provide evidence of ongoing training, risk mitigation and operational resilience required under many compliance frameworks.
How should organizations compare cybersecurity tools for compliance needs?
Evaluate tools against applicable standards such as NIST, HIPAA or PCI-DSS. Focus on visibility, documentation capabilities, reporting functions and integration with existing systems to ensure they support audit readiness and measurable control effectiveness.
How can cybersecurity compliance be automated?
Automation can streamline evidence collection, policy enforcement and reporting through continuous monitoring tools, centralized dashboards and predefined workflows. This reduces manual effort while improving accuracy and consistency.
How can organizations maintain compliance during new procurement?
Incorporate security requirements into vendor selection processes, require documented framework alignment and conduct third-party risk assessments before onboarding new suppliers or technology.
How can the compliance process be streamlined?
Centralize policies, standardize reporting and use structured frameworks supported by vCISO oversight to create repeatable, scalable compliance workflows.
Share This Story, Choose Your Platform!
Related Posts
What Enterprises Need To Know About Cyber Governance, Risk And Compliance
Learn all about cyber governance, risk and compliance in 2026 and why this must be a consideration at the highest levels of all organizations.
Navigating Essential Cybersecurity Compliance Standards: What To Know
There are a range of cybersecurity compliance standards firms of all sizes must deal with, including mandatory and voluntary frameworks. Here's what you need to know.
Understanding The Requirements Of Information Security Compliance
Learn precisely what information security compliance entails and the various steps that go into making this effective.
The Importance Of Effective Cybersecurity Services For Small Businesses
Find out why cybersecurity services for small businesses are more in-demand than ever as cybercriminals shift their focus to less-sizable enterprises.
Cybersecurity Compliance: What You Need Without Hiring A CISO
Find out what's required to ensure cybersecurity compliance and how this can be achieved without the need for a full-time CISO.
How Cybersecurity Startups Manage Compliance And Security Certifications
For cybersecurity startups, prioritizing compliance early builds trust, accelerates growth, and ensures security standards align with evolving threats and customer expectations.





