The Exfiltration Endgame
Anti Data Exfiltration: The 2015 Architectural Bet That Solved Ransomware
ADX Protect is the only enterprise security product built specifically for this control point.
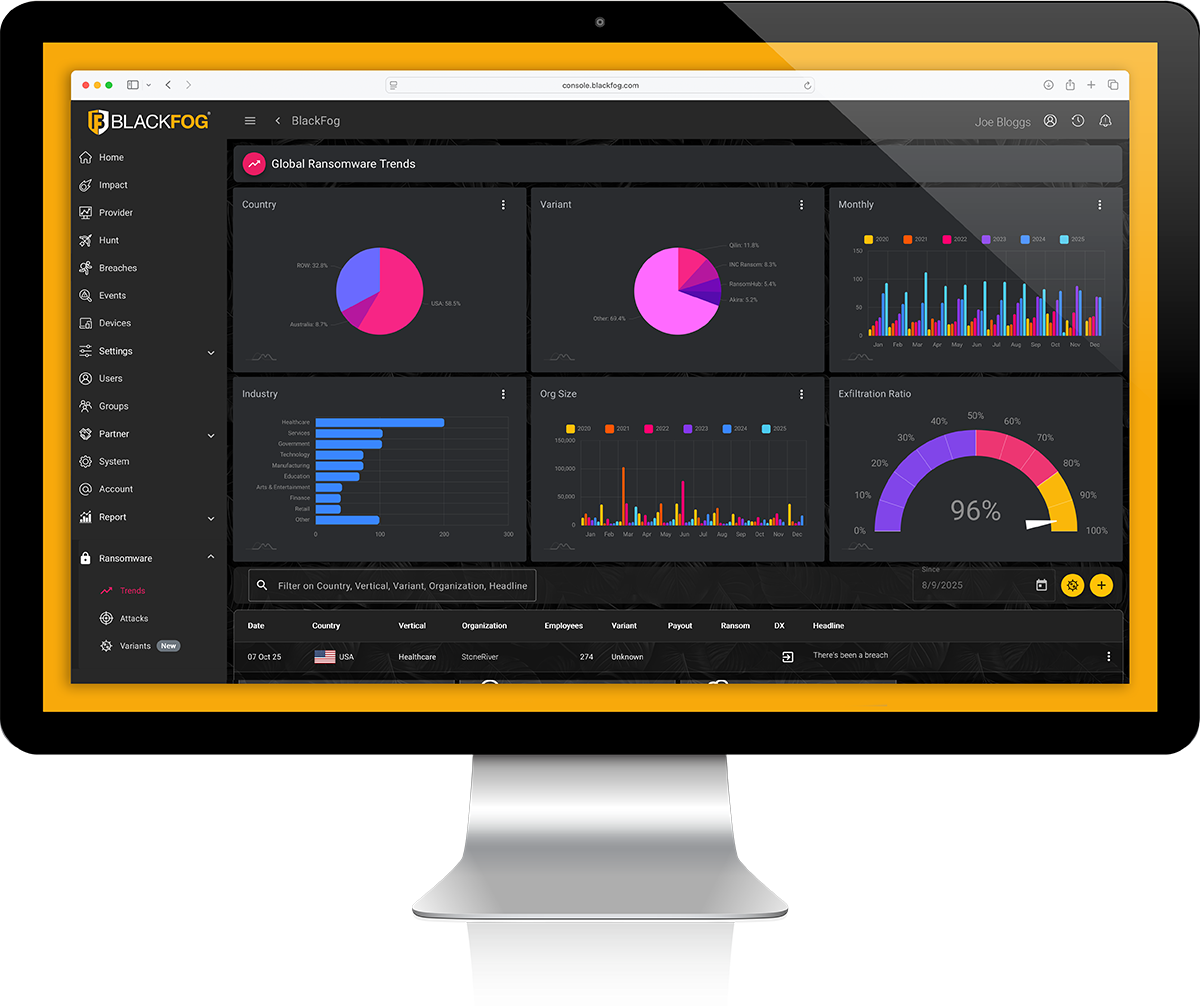
Backed by Industry-Defining Research
BlackFog’s 2025 State of Ransomware Report is the most comprehensive global tracker of ransomware activity, cited by CSO Online, Help Net Security, Cybersecurity Dive, and BleepingComputer.
*Source: BlackFog 2025 State of Ransomware Report.
Based on data collected from BlackFog Console deployments and global threat intelligence between January and December 2025.
The Arrival of Agentic AI Attacks
The third exfiltration vector arrived in 2025 and ADX Protect’s architecture was built for it.
Source: Anthropic threat intelligence disclosure, 2025.

Stop Data Exfiltration. Stop Cyberattacks.
Hackers don’t win when they break in, they win when they get data out. That’s why data exfiltration is the true endgame of every cyberattack.
BlackFog’s anti data exfiltration (ADX) technology blocks unauthorized transfers in real-time, ensuring your sensitive information never leaves your devices or network.
When the data stays inside, breaches fail, ransoms collapse, and your organization stays resilient.

How ADX Protect Stops the Exfiltration
One lightweight agent. Three coordinated layers of prevention. Built for the only control point that matters.
Centralized BlackFog Console. Multi-platform support. SOC 2 Type II certified.
Built for Real-World Enterprise Deployment
A single endpoint agent and a centralized console designed to run alongside your existing security stack without replacing it.
Compatible with CrowdStrike, SentinelOne, Microsoft Defender, Sophos, and most enterprise endpoint security stacks.