
ClawdBot went viral over the weekend of January 24-25, 2026, racking up 85,000 stars on GitHub and 11,500 forks within days. Security researchers started raising alarms almost immediately.
The open-source AI assistant promises to be “the AI that actually does things.” It reads files, executes shell commands, sends emails, manages calendars, and controls your browser. It remembers conversations for weeks. It also stores everything in plaintext files that any malware can read: API keys, OAuth tokens, chat histories, personal notes.
For attackers, ClawdBot is a gift. A single installation sits in a predictable directory with no encryption, holds credentials for every service the agent accesses, and the harsh reality is that your employees may have already installed it.
Not Your Typical Shadow AI
Most shadow AI conversations focus on employees pasting sensitive data into ChatGPT or other cloud-based tools. Samsung learned this the hard way in 2023 when engineers leaked source code, meeting transcripts, and chip testing sequences into ChatGPT within 20 days of getting access. That risk is real, but it requires active user behavior: someone has to copy and paste sensitive data into a browser window.
ClawdBot is different – it creates a passive data exfiltration risk.
It runs as an always-on autonomous agent with full system access, reading and writing files, executing shell commands, and connecting to email, messaging apps, and calendars. Every credential it needs gets stored in plaintext configuration files on the local disk. Every conversation flows through its memory system. The user doesn’t need to do anything wrong. The data basically accumulates automatically.
What Gets Stored and Where
ClawdBot stores its configuration in directories like ~/.clawdbot/, ~/clawd/, and more recently ~/.moltbot/ and ~/.openclaw/.
Inside these directories sit JSON and Markdown files containing API keys for OpenAI, Anthropic, and other LLM providers, OAuth tokens and bot secrets for Jira, Slack, GitHub, and any other service the agent integrates with, full conversation histories from private chats across WhatsApp, Telegram, and Discord, and persistent memory files like MEMORY.md and SOUL.md.
These memory files are particularly valuable for cybercriminals. They contain what the user is working on, who they communicate with regularly, their writing style, and personal context the agent uses to be helpful.
None of this is encrypted. There’s no use of the macOS Keychain or Windows Credential Manager. Everything sits in plaintext, readable by any process running on the system.
Infostealers Are Already Watching
The first problem is that the predictable file locations make ClawdBot an easy target for infostealer campaigns. Well-known malware-as-a-service families like RedLine, Lumma, and Vidar all include configurable file grabber modules that let operators specify custom directories and file patterns to sweep. Adding ~/.clawdbot/ or ~/clawd/ to an existing campaign takes minutes.
The stolen data goes beyond credential theft. Attackers get LLM provider API keys (which can rack up thousands in fraudulent charges), tokens for every integrated service, and the context to use those credentials convincingly. With access to a user’s memory files, an attacker knows exactly how to impersonate them.
Exposed Panels, Easy Exfiltration
The second problem is that malware isn’t the only way to steal ClawdBot data.
The gateway service binds to 0.0.0.0:18789 by default, exposing the control panel to any network interface. The exposure stems from an authentication bypass: ClawdBot’s gateway automatically trusts localhost connections without authentication.
Most deployments place the gateway behind nginx or Caddy on the same server, so all connections appear to come from localhost and get automatically approved. External attackers effectively get treated as local users.
As a result of this, a Censys search for “Clawdbot Control” in HTTP response bodies returns over 17,700 exposed instances:
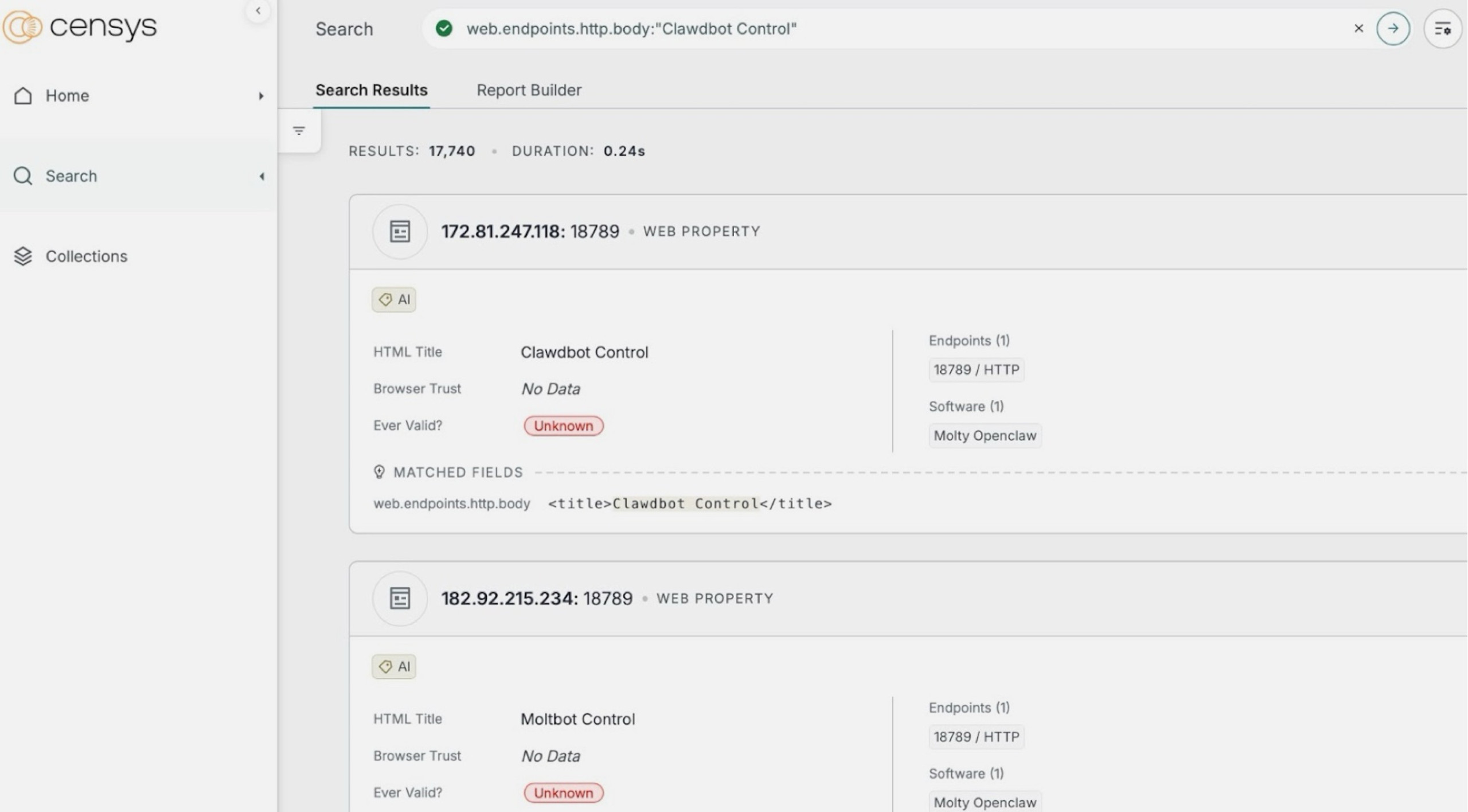
Figure 1: Censys search showing 17,740 exposed Clawdbot Control panels.
Anyone who connects to a misconfigured instance can sometimes access plaintext credentials, full conversation histories across all connected chat platforms, and the ability to send messages as the user. They can also execute commands on the host machine. For data theft purposes, this means attackers can exfiltrate everything ClawdBot has stored without ever touching the endpoint with malware.
Why Enterprises Should Worry
If even one employee connected ClawdBot to their work email, granted it access to corporate calendars, or stored company API credentials in its configuration files, you have an unmanaged data store containing sensitive corporate information. A single installation might hold Slack tokens, Jira API keys, VPN credentials, email OAuth tokens, and months of conversation history about internal projects.
The rebrand to Moltbot and then OpenClaw hasn’t changed the underlying storage model. The ~/.clawdbot/ directory path and CLAWDBOT_* environment variables remain for backward compatibility, so all three names point to the same exfiltration risk.
What Security Teams Should Do Now
If ClawdBot has made it into your environment, the main priority should be to understand your exposure and close the gaps before attackers exploit them. The challenge, however, is that traditional endpoint security wasn’t built for this threat.
DLP tools look for structured data patterns like credit card numbers, not JSON files full of API keys. Antivirus catches malware after execution, but by then, the ClawdBot directory has already been swept and staged for exfiltration.
Here’s where to start:
|
Step |
Action |
Why it matters |
|
1 |
Scan endpoints for ClawdBot directories (~/.clawdbot/, ~/clawd/, ~/.moltbot/, ~/.openclaw/) |
Establishes whether you have exposure in your environment |
|
2 |
Inventory what credentials and services were connected |
Determines blast radius if data was already exfiltrated |
|
3 |
Rotate any API keys, OAuth tokens, or secrets stored in ClawdBot configs |
Assumes compromise for anything the agent had access to |
|
4 |
Monitor for outbound connections to ClawdBot-related infrastructure |
Detects active exfiltration or C2 communication |
|
5 |
Block or alert on new ClawdBot installations going forward |
Prevents future exposure from employee adoption |
|
6 |
Review network logs for connections to port 18789 |
Identifies exposed control panels in your environment |
For ongoing protection, anti data exfiltration (ADX) technology addresses the gaps that traditional tools leave open. With 96% of ransomware attacks now involving data exfiltration, stopping unauthorized outbound transfers has become as important as blocking malware.
BlackFog’s ADX technology monitors outbound transfers and blocks unauthorized data from leaving endpoints in real time, regardless of whether the source is recognized malware or a legitimate application being abused.
For shadow AI specifically, ADX Vision provides visibility into tools like ClawdBot that employees install without approval, along with automated policy enforcement to prevent data leakage to LLM providers.
Get started today: https://www.blackfog.com/adx-protect-enterprise/.
Share This Story, Choose Your Platform!
Related Posts
Confronting INC Ransom: BlackFog’s Prevention-First Strategy for Affiliate-Driven Ransomware
Confronting INC Ransom, BlackFog’s Prevention-First Strategy for Affiliate-Driven Ransomware.
CamoLeak: How GitHub Copilot Became An Exfiltration Channel
CamoLeak (CVE-2025-59145) turned GitHub Copilot into a silent data exfiltration channel via prompt injection and GitHub's own image proxy. CVSS 9.6.
The State of Ransomware: March 2026
BlackFog's state of ransomware March 2026 measures publicly disclosed and non-disclosed attacks globally.
Venom Stealer Turns ClickFix Into a Full Exfiltration Pipeline
BlackFog analyzes Venom Stealer, a new MaaS infostealer that uses ClickFix delivery to launch an automated exfiltration pipeline covering credential theft, wallet cracking, and fund sweeping.
What Enterprises Need To Know About Cyber Governance, Risk And Compliance
Learn all about cyber governance, risk and compliance in 2026 and why this must be a consideration at the highest levels of all organizations.
Navigating Essential Cybersecurity Compliance Standards: What To Know
There are a range of cybersecurity compliance standards firms of all sizes must deal with, including mandatory and voluntary frameworks. Here's what you need to know.






