
In April 2025, DaVita, one of America’s largest kidney dialysis providers, was hit by a ransomware attack that leaked the personal and medical data of 2.7 million patients. DaVita runs over 2,600 outpatient dialysis centers across the United States, treating roughly 200,000 patients who rely on regular dialysis to stay alive.
What Happened? Timeline of the DaVita Incident
The DaVita ransomware attack played out over nearly three weeks. Cybercriminals first gained access to DaVita’s network on March 24, 2025. They moved through systems undetected until April 12, 2025, when DaVita’s security team spotted the intrusion.
Two days later, DaVita filed an 8-K report with the SEC, publicly confirming the cyberattack. The company said that while internal operations took a hit, patient care kept running thanks to backup plans.
By April 24, the attackers posted stolen data on their leak site. DaVita spent weeks piecing together what had been taken, and by June 18, 2025, they confirmed that sensitive patient data from their dialysis labs database had been exposed.
Scale of Impact: Millions of Patients Affected
When DaVita first filed breach notices with state attorneys general, the numbers suggested just over one million people had been affected. State-level reports varied: Texas reported 81,740 individuals, Washington 13,404, South Carolina 11,570, Massachusetts 7,829, and Montana 761, according to attorney general disclosures.
The federal picture was much larger. By August 2025, the U.S. Department of Health and Human Services put the final count at 2,689,826 individuals. The discrepancy comes down to timing: forensic reviews take months to complete, and not all states publicly release their numbers.
The DaVita dialysis ransomware attack victims span dozens of states, and many are still receiving notification letters months after the incident. At 2.7 million records, this ransomware attack on DaVita is one of the largest healthcare data breaches reported to HHS in 2025.
What Data Was Compromised and Why It Matters
The ransomware attack DaVita suffered gave cybercriminals access to the dialysis laboratory database. They walked away with sensitive patient information, including:
- Names, addresses, and dates of birth
- Social Security numbers
- Health insurance details and policy information
- Medical records including treatment info and dialysis test results
- Tax identification numbers
- Images of checks written to DaVita
This kind of healthcare data is extremely valuable for cybercriminals. It can be used for identity theft, insurance fraud, and even fake prescription schemes. Unlike a stolen credit card number, you can’t just cancel your medical history and get a new one.
Under HIPAA’s Breach Notification Rule, healthcare organizations must notify affected individuals, HHS, and the media within 60 days of discovering a breach involving 500 or more people. DaVita began mailing notification letters on August 5, 2025.
The Spotlight on Interlock Ransomware
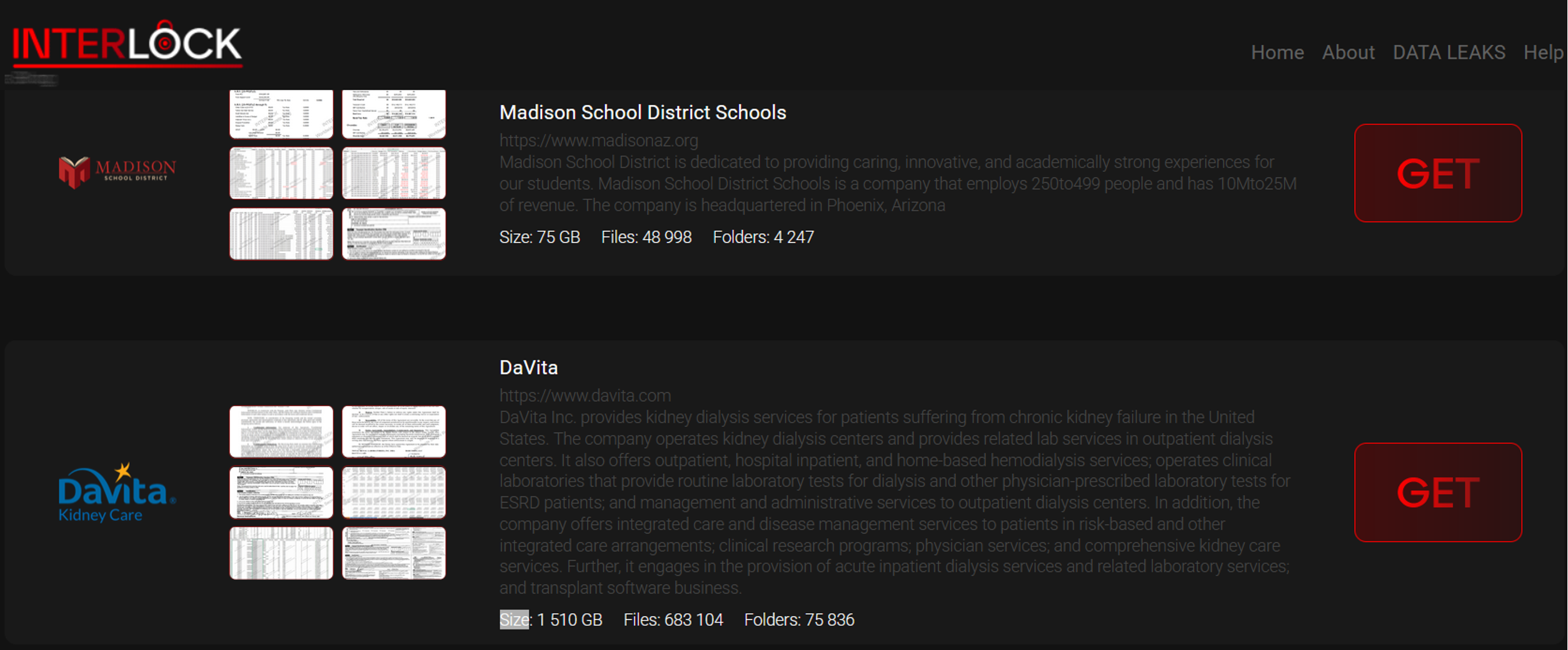
The Interlock ransomware group claimed the DaVita attack, posting proof on their dark web leak site and bragging about stealing 1.5 TB of data. Interlock showed up in September 2024 and has quickly built a reputation for going after healthcare targets.
Their playbook is double extortion: steal the data first, then lock up the systems. Victims get squeezed from both sides, pressured to pay not just to unlock their files but to keep their stolen data from going public.
In July 2025, the FBI, CISA, HHS, and MS-ISAC put out a joint warning about Interlock. The advisory called out the group’s unusual techniques, including drive-by download attacks that look like legitimate browser updates and the ClickFix trick, which fools users into running malicious commands.
Interlock has hit other healthcare organizations this year too, including Kettering Health in Ohio and Texas Tech University Health Sciences Center.
DaVita’s Response: Containment and Remediation
DaVita’s priority was keeping dialysis patients alive while dealing with the attack. When they detected the breach on April 12, the company pulled affected systems offline and brought in outside cybersecurity help.
Here’s what they did:
- Shut down parts of the network to stop the spread
- Switched to manual processes so dialysis treatments could continue
- Rebuilt and restored encrypted systems from the ground up
- Filed disclosures with the SEC and state attorneys general
- Offered 12-24 months of free credit monitoring to affected patients
Unfortunately, the financial damage was severe. DaVita reported about $13.5 million in costs tied to the incident during Q2 2025, covering forensic investigations and patient protection services. The latest DaVita ransomware attack update shows ongoing impacts to billing and revenue collection.
Broader Healthcare Cybersecurity Trends
The ransomware attack on DaVita fits a pattern that’s been building for years. In Q3 2025, healthcare was the most targeted sector, accounting for 32% of all publicly disclosed attacks with 86 incidents in the quarter alone.
Hospitals and clinics run systems that people’s lives depend on, which makes them more likely to pay up fast. They also sit on massive amounts of personal data, and plenty still run older technology with known weaknesses.
The 10 largest healthcare breaches of 2025 affected more than 20 million Americans combined.
Lessons from the DaVita Ransomware Attack
The DaVita breach is a harsh reminder that size and resources don’t make an organization untouchable. For the DaVita dialysis ransomware attack victims, this means staying alert for suspicious activity on their accounts and credit reports.
For healthcare organizations, the Davita ransomware attack shows why waiting for an attack to happen is a losing strategy.
Some of the main incident response lessons point to the need for network segmentation, real-time monitoring, and training staff to spot social engineering attempts. But with over 96% of ransomware attacks now involving data exfiltration, the best cybersecurity practice in this context is to stop data from leaving your network in the first place.
BlackFog’s ADX platform uses AI based anti data exfiltration technology to block ransomware at the source, preventing unauthorized data from ever leaving your endpoints. Rather than relying on detection after a breach occurs, ADX proactively monitors and blocks suspicious outbound traffic in real time, neutralizing threats like Interlock before they can extract sensitive patient data.
Learn more here: ADX Protect.
Share This Story, Choose Your Platform!
Related Posts
DaVita Ransomware Attack: 2.7M Affected in Major Data Breach
The DaVita ransomware attack exposed 2.7 million patient records. Learn what happened, what data was stolen, and how the Interlock gang pulled it off.
Confronting INC Ransom: BlackFog’s Prevention-First Strategy for Affiliate-Driven Ransomware
Confronting INC Ransom, BlackFog’s Prevention-First Strategy for Affiliate-Driven Ransomware.
CamoLeak: How GitHub Copilot Became An Exfiltration Channel
CamoLeak (CVE-2025-59145) turned GitHub Copilot into a silent data exfiltration channel via prompt injection and GitHub's own image proxy. CVSS 9.6.
The State of Ransomware: March 2026
BlackFog's state of ransomware March 2026 measures publicly disclosed and non-disclosed attacks globally.
Venom Stealer Turns ClickFix Into a Full Exfiltration Pipeline
BlackFog analyzes Venom Stealer, a new MaaS infostealer that uses ClickFix delivery to launch an automated exfiltration pipeline covering credential theft, wallet cracking, and fund sweeping.
What Enterprises Need To Know About Cyber Governance, Risk And Compliance
Learn all about cyber governance, risk and compliance in 2026 and why this must be a consideration at the highest levels of all organizations.





