
Developing A Ransomware Backup Strategy Your Business Can Trust
Dealing with today’s ransomware threats requires a comprehensive, defense in depth approach. While preventing attacks should always be the top priority, no solution is infallible. As threat actors evolve their tactics and find new ways to breach networks, businesses must build resilience through layered protection.
A key part of this is having a clear and well-defined remediation plan in place to reduce disruption and downtime if an attack succeeds. What’s more, a fast, secure and reliable backup strategy is one of the most critical components. When executed properly, this ensures business continuity, preserves data integrity and removes the pressure to pay, even in worst-case ransomware scenarios.
Why Backups Are Essential To Ransomware Protection Resilience
Ransomware is designed to cause maximum disruption by targeting mission-critical systems and shutting down key operations, whether this is manufacturing, shipping or processing key financial data. When operations grind to a halt, businesses face financial losses, reputational damage and regulatory consequences.
In 2025, attacks like the ones on Jaguar Land Rover (JLR) and Marks and Spencer (M&S) led to major disruption. In JLR’s case, production was suspended for around a month, causing an estimated £1.9 billion hit to the UK’s economy, while M&S was forced to suspend online orders for months, effectively wiping out its profits for the first half of the year.
These examples show how even well-resourced companies can be brought to a standstill. Threat actors use this disruption as leverage, knowing firms are under intense pressure to pay quickly. However, even paying the ransom offers no guarantee. Decryption keys may be faulty, data may remain missing and attackers are likely to strike again.
Reliable, well-protected backups are the only dependable way to recover. They restore access to essential systems without giving in to extortion and are central to any serious ransomware resilience strategy.
Core Considerations For Effective Backups
Backup strategies must be built for resilience. Securely storing data is only part of the equation. Companies must also be able to restore it quickly and confidently if ransomware strikes. A proven framework for this is the 3-2-1-1 rule, which breaks down as follows:
- 3 copies of your data: One primary and two backups.
- 2 different storage types: For example, on-prem hardware and cloud.
- 1 offsite copy: Stored away from the production environment to avoid cross-contamination.
- 1 immutable or air-gapped copy: A backup that cannot be altered or deleted, even by attackers with privileged access.
This structure helps ensure both redundancy and recovery integrity, even in complex ransomware scenarios. However, within this framework, there are a range of potential solutions that businesses can turn to in order to meet these requirements, so it’s important to be aware of the pros and cons of each. Common backup options include:
- Local backups: Fast and cost-effective, but vulnerable to ransomware if not properly segmented or secured.
- Offsite physical backups: Provide isolation, but can be slower to recover from and require manual handling.
- Cloud-based backups: Scalable and accessible, but may depend on the provider’s security model and can introduce latency.
- Immutable backups: Cannot be altered or deleted, offering strong protection against ransomware tampering.
- Continuous backups: Reduce data loss between scheduled snapshots, but may require more storage and bandwidth.
When forming a backup plan, businesses must strike the right balance between fast recovery, acceptable recovery point objectives (RPOs) and cost. Choosing the right mix is essential to ensure continuity without unnecessary complexity.
Securing Your Backup Infrastructure Against Ransomware
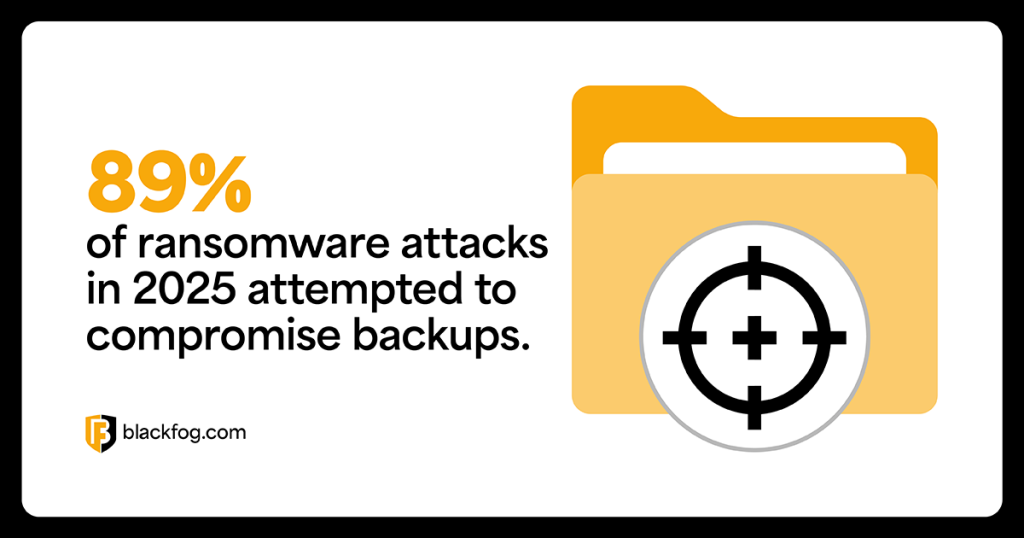
Ransomware groups know good backups reduce the incentive to pay. That’s why, as well as switching to tactics like double extortion ransomware, they increasingly target backup systems directly to prevent recovery and force payment. In fact, research from Veeam claims 89 percent of ransomware attacks in 2025 attempted to compromise backups.
Without secure, isolated backups, recovery becomes difficult or even impossible. That’s why backup infrastructure must be fully protected by the same ransomware prevention strategies applied to primary systems. This includes strong access controls, network segmentation, continuous monitoring and behavioral analytics to detect early-stage threats.
Backup environments are often overlooked or assumed to be safe by default, making them an attractive target. Any backup system connected to your network should be treated as part of your security perimeter.
Common Mistakes That Undermine Backup Strategies
A well-designed backup strategy is only effective if it works when it’s needed most. Yet many businesses discover too late that their backups are incomplete, outdated or compromised. The following common errors can undermine even the most well-intentioned plans and lead to critical failures during a ransomware attack:
- Infrequent backups: Long gaps between backup cycles increase the risk of data loss. Use automation to maintain consistent backup intervals.
- No testing or validation: Backups must be regularly tested to ensure they can be restored quickly and fully under pressure.
- Overreliance on cloud providers: Not all cloud backups are immutable or secure by default. Understand your provider’s controls and limitations.
- Single storage location: Keeping all backups in one environment increases exposure. Always maintain offsite and segmented copies.
- Poor access controls: Broad or default access can allow ransomware to reach backup systems. Enforce strict, role-based permissions.
Building A Recovery-Ready Backup Plan
An effective ransomware backup strategy is only as strong as the recovery plan behind it. Businesses must go beyond storing data and ensure they can restore operations quickly, confidently and without delays. Key questions to ask include:
- What is your most critical data and where is it stored?
- How quickly do systems need to be restored to maintain operations?
- What are your acceptable recovery time objectives (RTO) and RPOs?
- Who is responsible for managing backups, monitoring their integrity and leading recovery efforts in a crisis?
Answering these questions clearly before an attack occurs ensures backup strategies are aligned with business needs and that the right people are in place to act when it matters most.
Share This Story, Choose Your Platform!
Related Posts
Steaelite RAT Enables Double Extortion Attacks from a Single Panel
Steaelite is a newly emerging RAT that unifies credential theft, data exfiltration, and ransomware in a single web panel, accelerating double extortion attacks.
ClawdBot and OpenClaw: When Local AI Becomes A Data Exfiltration Goldmine
ClawdBot stores API keys, chat histories, and user memories in plaintext files, and infostealers like RedLine, Lumma, and Vidar are already targeting it.
West Harlem Group Assistance Stops Ransomware and Cryptojacking with BlackFog ADX
West Harlem Group Assistance secures its community mission by preventing ransomware and cryptojacking with BlackFog ADX.
Why Traditional Security Fails To Deal With Advanced Persistent Threats
Learn why advanced persistent threats remain a growing cybersecurity risk in 2026 and where organizations must focus to address them.
What Does Advanced Threat Protection Really Mean In 2026?
Find out why businesses need advanced threat protection to cope with the new era of sophisticated, persistent cyber risks.
How Can You Prevent Viruses And Malicious Code Today?
Preventing viruses and malicious code is harder than ever in a landscape where APTs are a growing threat. Here's what you need to know to stay safe.






