
In 2025, Oracle became the center of three security incidents that collectively exposed millions of records, compromised patient health data across dozens of hospitals, and gave cybercriminals a direct line to enterprise credentials.
The breaches spanned Oracle Cloud’s authentication infrastructure, legacy Cerner healthcare servers, and the Oracle E-Business Suite, affecting organizations across finance, healthcare, education, and government.
The Oracle data breach stands as one of the clearest examples, yet of what happens when legacy infrastructure, delayed patching, and third-party software dependencies converge.
With data exfiltration at the center of all three incidents, the attacks also show us why traditional perimeter defenses continue to fall short against the latest threats.
What Was the Oracle Breach? A Timeline of Events
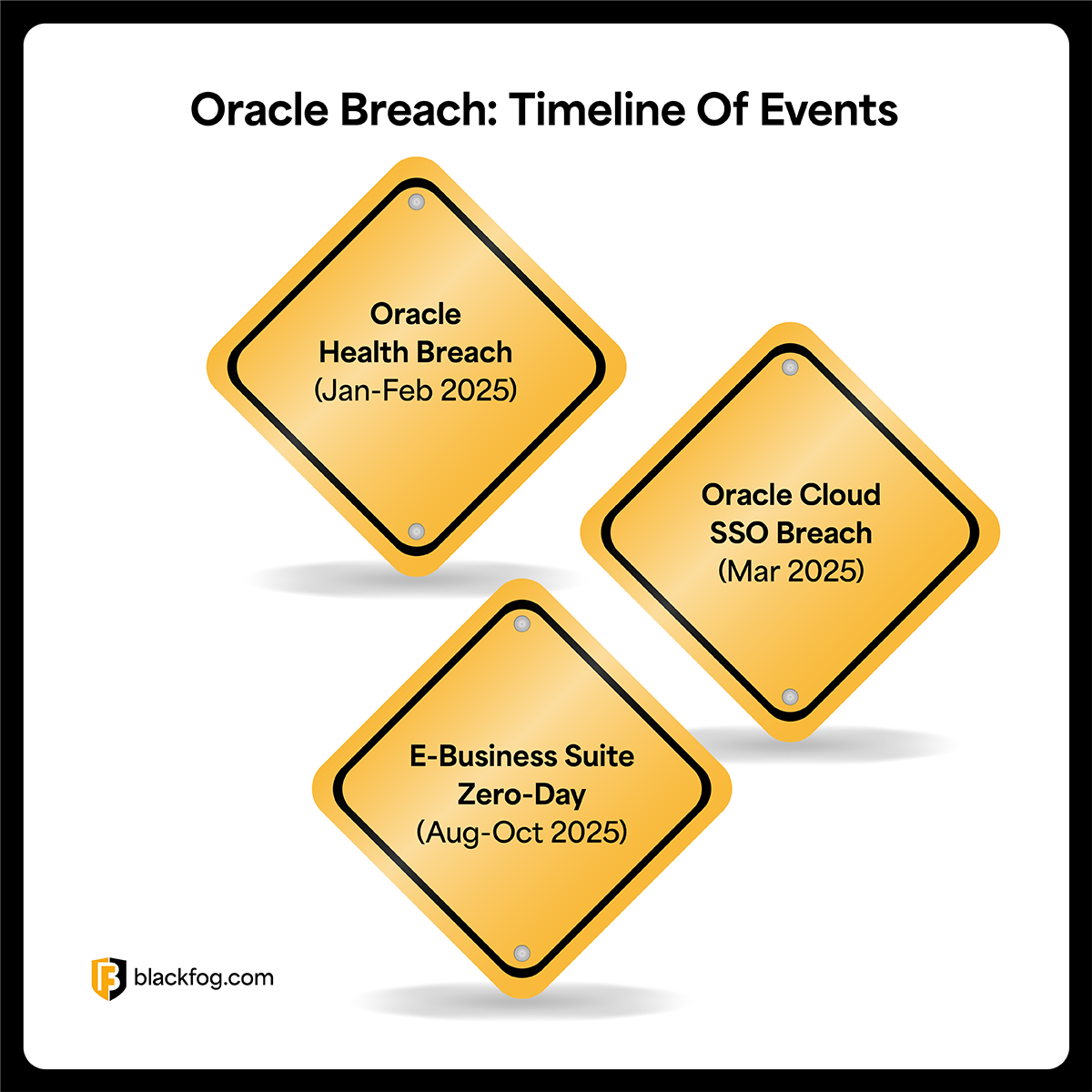
The first signs of trouble surfaced in early 2025, and over the following months, three separate incidents unfolded across Oracle’s infrastructure.
1. Oracle Health breach (Jan–Feb 2025)
An unknown threat actor used stolen credentials to access legacy Oracle Health (formerly Cerner) servers that had not yet been migrated to Oracle Cloud. The breach went undetected until February 20, when Oracle Health identified the intrusion and began notifying affected healthcare providers.
2. Oracle Cloud SSO breach (Mar 2025)
A threat actor operating under the alias “rose87168” exploited a vulnerability in Oracle Cloud’s Single Sign-On (SSO) and Lightweight Directory Access Protocol (LDAP) systems. By March 21, CloudSEK’s XVigil platform discovered the attacker selling approximately 6 million records on BreachForums, with data allegedly impacting over 140,000 Oracle Cloud tenants. The attacker demanded over $200 million in Monero from Oracle directly. When Oracle refused to engage, samples of the stolen data appeared on underground forums.
3. E-Business Suite zero-day (Aug–Oct 2025)
The Clop ransomware group exploited a zero-day exploit (CVE-2025-61882) in Oracle’s E-Business Suite, quietly exfiltrating data from enterprise environments for weeks before launching a mass extortion campaign on September 29. Oracle released emergency patches in early October, but by then Clop’s leak site had already begun naming victims.
How Did the Oracle Breach Happen?
Each incident exploited a different weakness, but a common thread runs through all three: unpatched or outdated infrastructure that gave attackers a clear path to sensitive data.
The Oracle Cloud data breach leveraged CVE-2021-35587, a vulnerability in Oracle Access Manager added to CISA’s Known Exploited Vulnerabilities catalog in late 2022. CloudSEK’s investigation found the compromised endpoint was running Oracle Fusion Middleware 11G, a version not updated since 2014. Despite Oracle’s initial denial that any breach had occurred, multiple security researchers verified the Oracle credential breach by confirming the legitimacy of the leaked data.
The Oracle Health breach took a simpler path. Attackers used stolen credentials to access legacy Cerner data migration servers that predated Oracle’s $28.3 billion acquisition of Cerner in 2022.
The E-Business Suite attack was the most complex. Clop exploited a previously unknown vulnerability in the UiServlet component, exfiltrating documents at scale. Mandiant’s analysis identified exploitation activity dating back to July 2025, weeks before any patch was available.
Who Was Affected? Industries at Risk
The scope of these incidents extends across virtually every sector.
The Oracle Cloud breach potentially exposed authentication data for over 140,000 tenants. Compromised data included Java KeyStore (JKS) files, encrypted SSO and LDAP passwords, and Enterprise Manager JPS keys, giving attackers a path to lateral movement across interconnected systems.
The Oracle Health breach hit healthcare particularly hard. Up to 80 hospitals were affected, with exposed patient data including:
- Names and Social Security numbers
- Clinical test results and diagnoses
- Treatment records and physician details
Munson Healthcare alone confirmed over 100,000 patients were impacted, and multiple class action lawsuits have since been filed. Oracle data breach settlement proceedings remain ongoing.
Clop’s E-Business Suite campaign cut across industries. Some of the named victims include Harvard University, The Washington Post, Schneider Electric, Logitech, and Envoy Air. Cybersecurity analysts estimate over 100 companies may have been compromised in total.
Why the Oracle Breach Is a Wake-Up Call
These incidents surface cloud security risks that extend well beyond Oracle. Organizations depend on intricate vendor ecosystems where a single vulnerability can cascade across thousands of customers, and even major cloud providers can harbor unpatched legacy components.
Oracle Health asked healthcare providers to delay patient notifications while law enforcement investigated, and the months-long gap between breach discovery and vulnerability disclosure raises serious questions about incident transparency under HIPAA. Organizations that fail to meet notification timelines risk regulatory penalties under data protection laws, and Oracle’s approach has prompted calls for stricter cybersecurity compliance standards.
Clop’s exploitation of the E-Business Suite follows a pattern the group has used before: find a widely deployed third-party platform, exfiltrate data from as many organizations as possible, then extort. The consistent factor across every Clop campaign is data exfiltration. The group does not encrypt systems. It steals data and leverages it for extortion, which means traditional perimeter defenses miss the actual threat entirely.
According to BlackFog’s 2025 State of Ransomware report, 96% of disclosed ransomware attacks now involve data exfiltration, making it the dominant tactic worldwide.
What Should Businesses Do Now?
Organizations that use any Oracle product should think about treating these breaches as a trigger for immediate action.
1. Rotate employee credentials immediately
Any organization using Oracle Cloud’s SSO or LDAP systems should reset passwords, regenerate SASL/MD5 hashes, and replace affected certificates. Multi-factor authentication should be enforced across all Oracle-integrated access points.
2. Review third-party access and exposure
Audit which Oracle products are deployed across your environment, check patch levels against Oracle’s Critical Patch Update advisories, and verify that legacy components like Fusion Middleware 11G have been upgraded or decommissioned. Threat intelligence feeds that track active exploitation of Oracle vulnerabilities can help prioritize patching.
3. Monitor egress traffic for data exfiltration
Clop’s attack succeeded because data left the organization undetected for weeks. Tools that inspect outbound network behavior and flag anomalous transfers, like anti data exfiltration (ADX) technology, can catch what perimeter defenses miss.
4. Implement zero-trust access controls
Restrict lateral movement, enforce least-privilege policies, and segment sensitive systems so that a single compromised credential cannot unlock the entire environment.
5. Pressure-test your incident response plan
Run a tabletop exercise that simulates a third-party breach where the vendor controls the timeline, and make sure your team, whether internal or through an MSP, knows how to detect and respond independently.
Lessons Learned From the Oracle Breach
The Oracle security breach reinforces several uncomfortable truths.
Perimeter security alone is not enough when attackers are inside the supply chain. Patch management failures at the vendor level can expose customers who assumed their cloud provider was handling security on their behalf. Data exfiltration, not ransomware encryption, is becoming more common as the endgame of attacks.
The shift toward preventing data from leaving the environment, regardless of how attackers got in, is where enterprise security needs to go. Continuous monitoring, real-time visibility into data movement, and on-device protections that stop exfiltration at the source are the controls that would have mattered most across all three Oracle incidents.
Is Your Organization Prepared?
Zero-day vulnerabilities are increasing in frequency, third-party software dependencies are expanding, and attackers are getting faster at turning access into exfiltration. The organizations that fare best are the ones that have already accepted that prevention must extend beyond the perimeter, all the way to the data itself.
Learn more about how BlackFog prevents data exfiltration and keeps organizations protected from the threats that traditional security tools miss.
Share This Story, Choose Your Platform!
Related Posts
Oracle Breach: What Happened and Why It Matters
The 2025 Oracle breach exposed millions of records across three separate incidents. Learn how attackers got in, which industries were hit, and how to protect your organization.
What Is An Integrity Data Breach?
Find out what an integrity data breach involves, how it differs from data loss and why it's vital for businesses to be aware of the potential risks.
How Quickly Should A Suspected Data Breach Be Reported?
Data breach reporting deadlines can be tight. Learn when firms must report a suspected data breach, who must be informed and the risks of delay.
What Are The 5 Most Common Sources Of Data Leaks On The Internet?
Understanding how these five common sources of data leaks occur and how they can be prevented is an essential part of a data security strategy.
What Are The Latest Major Data Breaches And What Was Leaked?
These ten major data breaches from 2025 highlight the worldwide scale of cybersecurity incidents in the past year.
How Can A Company Develop An Effective Data Breach Response Plan?
Learn how to build an effective data breach response plan with clear roles, rapid detection, containment procedures and tested communication protocols.





