
Why Exfiltration of Data is the Biggest Cyberthreat Facing Your Business
Loss or exposure of data is one of the most costly issues facing any business today. A typical incident can quickly run into millions of dollars worth of costs to rectify and recover, so it’s no wonder that data breach prevention has become a top priority for businesses.
While accidental loss or exposure remain issues, one particular danger is the deliberate exfiltration of data. This is often a key goal of ransomware attacks, as once cybercriminals have information, they have many options. Often, this involves extorting money from the business or selling valuable personal and financial data on the dark web.
The Danger of Data Exfiltration
As well as direct costs in the form of ransom payments, exfiltration of data can lead to many other issues. It can cause a major loss of trust among consumers, damaging a firm’s reputation for years to come. In turn, this means lost business and lower growth, and could even threaten the future viability of the company.
The consequences of data exfiltration can be severe and wide-ranging. For starters, it can do huge damage to any company’s reputation. Customers will take note that their data is not safe with the business and be very wary of handing over personal and financial information in the future.
On top of this, there is the increased risk of regulatory and legal action. Under GDPR, for example, fines for mishandling or losing data can reach either €20 million or four percent of a firm’s global turnover – whichever is higher. Regulators have already proven they aren’t afraid to use these powers, with the €1.2 billion fine handed out to Meta by Ireland’s data protection body in 2023 the largest penalty so far.
Firms also run the risk of giving away trade secrets or other proprietary information to competitors, which could set back future plans and lead to the loss of any competitive edge.
What Are The Key Trends In Data Exfiltration?
Recent trends have made it clear that data exfiltration has become the primary goal of many ransomware attacks, as opposed to activities such as encrypting data. Indeed, in 2025, data exfiltration was a goal in 96 percent of attacks. Therefore, it’s vital firms are up to speed on what this means for their cybersecurity strategy.
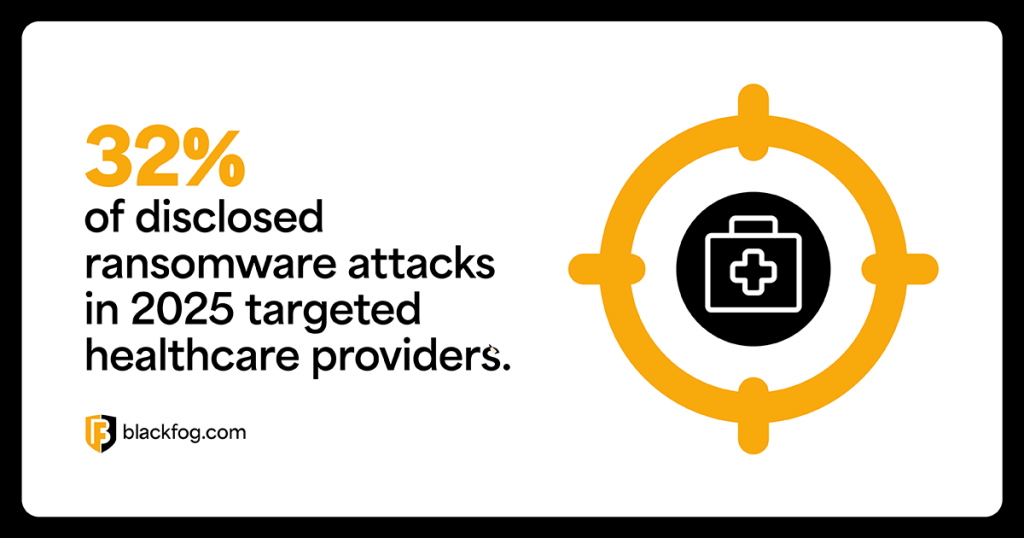
A key trend of 2025 was the targeting of key sectors that hold highly-sensitive data, such as healthcare, government and education. In Q3 of 2025, almost a third of publicly-disclosed attacks (32 percent) focused on the healthcare sector.
The tactics used by threat actors once they have exfiltrated data are also evolving, with groups becoming more aggressive in how they pressure victims into paying. For example, in one high-profile incident in the UK that saw the personal details of children stolen, criminals contacted parents by phone.
One reason for this may be that fewer companies are paying. According to research by Coveware, only 23 percent of ransomware victims paid attackers in Q3 2025, a record low. This may indicate that companies are becoming more confident in standing up to threats, even if this increases the risk of data exposure and reputational damage.
This emphasizes the importance of having data loss prevention strategies, rather than a reactive approach. If threat actors aren’t able to exfiltrate data in the first place, these dangers are avoided.
How Do Threat Actors Steal Data?
There are a wide range of methods ransomware groups can use to attack businesses and exfiltrate data, but the simplest often prove the most effective. Many breaches are the results of techniques such as a phishing attack, relying on errors by employees to give hackers access, such as by inadvertently sharing passwords or downloading malware.
Once inside, cybercriminals often aim to move laterally and use ‘low-and-slow’ methods of data exfiltration, such as DNS exfiltration, to avoid detection. This allows them to remove potentially large quantities of data over a long period of time.
It’s therefore important that enterprise data loss prevention solutions are able to spot such activities and block them as early as possible in order to prevent data being removed from the network.
What Types Of Data Exfiltration Do Organizations Currently Experience?
There are several types of data exfiltration that businesses need to be aware of. While deliberate, malicious data theft conducted via malware is often viewed as the most dangerous, it’s not the only way in which data loss occurs.
Many data breaches are the result of an insider threat, which could be either accidental or deliberate. For example, this could involve sending outbound emails to untrusted recipients, copying sensitive data onto external devices such as USB sticks to be physically removed from an office, or the use of unsecured and unauthorized tools like consumer cloud services to store data. To counter this, it’s important to have a clear and comprehensive data loss prevention policy that helps inform employees about their responsibilities and sets out what is and is not acceptable behavior when handling sensitive information.
How To Detect And Prevent Data Exfiltration
Legacy security tools such as firewalls were designed to keep threats out, not to detect malicious activity already inside the network. As a result, they are often ineffective at preventing data breaches, which increasingly originate from compromised users, endpoints or trusted services operating behind the perimeter. Detecting and preventing data exfiltration today requires inward-looking visibility and the ability to act as data is being stolen.
Essential best practices include:
- Real-time monitoring and response: Continuously inspect outbound traffic and data flows so suspicious transfers can be blocked immediately, limiting the amount of data an attacker can remove.
- Behavioral monitoring: Establish baselines of normal user and system behavior to flag anomalies such as unusual access patterns, unexpected data volumes or unfamiliar destinations.
- Network segmentation: Isolate systems and sensitive data stores to restrict lateral movement and reduce the pathways available for data to be aggregated and exfiltrated.
- Access controls: Enforce least-privilege access so users and applications only interact with the data they genuinely need, reducing exposure if credentials are compromised.
- Employee education: Train staff to recognize social engineering and risky data-handling behaviors that often enable exfiltration, whether intentional or accidental.
What Controls Help Defend Against Exfiltration Of Data?
There are dedicated solutions firms can turn to in order to protect against data loss, although businesses need to be certain they have the latest and most advanced defenses in order to block data theft without disrupting normal business operations.
Data loss prevention tools, for example, sound good, but they can come with their own problems. Legacy tools often take a data-centric approach, looking for key fingerprints that can suggest malicious activity. However, these solutions often find it hard to understand context or user intent, which can make them prone to disruptive false positives, while letting actual data theft through.
How Does BlackFog Prevent Data Exfiltration?
Dedicated anti data exfiltration (ADX) technology works differently. BlackFog’s approach takes a behavioral-focused attitude towards data traffic to build up a full picture of what normal activity looks like. This allows ADX to step in automatically to block any data theft attempts without the need for human intervention, and without getting in the way of legitimate traffic.
As an endpoint solution, this also ensures all activities are carried out on the device level, meaning there is no break in the security chain, as data does not need to be routed via a centralized solution for analysis. This gives the software a much smaller footprint than other data exfiltration prevention solutions, making it lightweight enough to be deployed on mobile devices outside the main network. As a result, businesses are better protected at all times, helping counter the growing risks posed by ransomware.
Share This Story, Choose Your Platform!
Related Posts
The State of Ransomware: February 2026
BlackFog's state of ransomware February 2026 measures publicly disclosed and non-disclosed attacks globally.
Steaelite RAT Enables Double Extortion Attacks from a Single Panel
Steaelite is a newly emerging RAT that unifies credential theft, data exfiltration, and ransomware in a single web panel, accelerating double extortion attacks.
ClawdBot and OpenClaw: When Local AI Becomes A Data Exfiltration Goldmine
ClawdBot stores API keys, chat histories, and user memories in plaintext files, and infostealers like RedLine, Lumma, and Vidar are already targeting it.
West Harlem Group Assistance Stops Ransomware and Cryptojacking with BlackFog ADX
West Harlem Group Assistance secures its community mission by preventing ransomware and cryptojacking with BlackFog ADX.
Why Traditional Security Fails To Deal With Advanced Persistent Threats
Learn why advanced persistent threats remain a growing cybersecurity risk in 2026 and where organizations must focus to address them.
What Does Advanced Threat Protection Really Mean In 2026?
Find out why businesses need advanced threat protection to cope with the new era of sophisticated, persistent cyber risks.






