The Importance Of A Data Breach Response Plan: Essential Management Steps
Cyberattacks are growing in scale and sophistication, with ransomware and data breaches now representing some of the most severe threats businesses face. The consequences of a successful attack have never been more significant. Beyond the immediate financial impact of operational downtime and recovery costs, organizations face regulatory fines, legal liability and lasting damage to customer trust.
Even businesses with the most robust security posture cannot guarantee they will never fall victim to an attack. Threat actors are constantly evolving their tactics, while even the most advanced safeguards cannot guarantee 100 percent protection from issues like human error. Having a clear, rehearsed plan in place ensures that when – not if – an incident does occur, it can be contained swiftly, before crucial data is lost. In turn, this can mean the difference between a contained disruption and a catastrophic event with far-reaching consequences.
What Is A Data Breach Response Plan?
A data breach response plan is a structured, documented framework that defines exactly how an organization should respond when unauthorized parties gain access to sensitive data. It covers everything from the moment a breach is detected through containment, investigation, notification and recovery, setting out essential steps and individual responsibilities at each stage.
This should be distinguished from broader incident response preparation. While incident response addresses any security event, a breach response plan specifically focuses on those that involve the compromise of personal or sensitive data, where regulatory notification obligations and legal accountability come into play.
As threats grow and the data firms hold gets increasingly extensive, this is becoming more important than ever. Cybercriminals increasingly make data exfiltration a key aim of their attacks, as it is highly valuable in threats like double extortion ransomware. Indeed, according to Verizon, ransomware attacks rose 37 percent year-over-year in 2025 and was present in 44 percent of all confirmed breaches.
The sheer volume of personal data firms now hold also raises the stakes. Large-scale breaches, such as the 2024 National Public Data cyberattack, can expose billions of records, illustrating how a single incident can compromise data on a huge scale.
“In most modern breaches, the real risk begins when data starts to move. Effective response plans are built around detecting and stopping exfiltration at the earliest possible stage.”
– Darren Williams, CEO and Founder, BlackFog
Why Every US Business Needs A Formal Breach Response Strategy
Firms operating in the US must be particularly focused on having a response plan, as the regulatory landscape facing these businesses is highly complex. All 50 states have enacted security breach notification laws and businesses must navigate these alongside a growing body of federal requirements spanning specific sectors including healthcare, financial services and critical infrastructure.
A growing number of states now mandate notification within 30 days of discovering a breach and penalties for missing those deadlines can be severe, including civil fines, attorney general enforcement actions and mandatory third-party auditing.
Without a tested response plan, meeting those obligations under the pressure of an active incident becomes extremely difficult. The consequences of falling short extend beyond regulatory fines. Customers who lose trust in a business following a poorly managed breach rarely return, and the reputational damage can outlast the financial penalties by years.
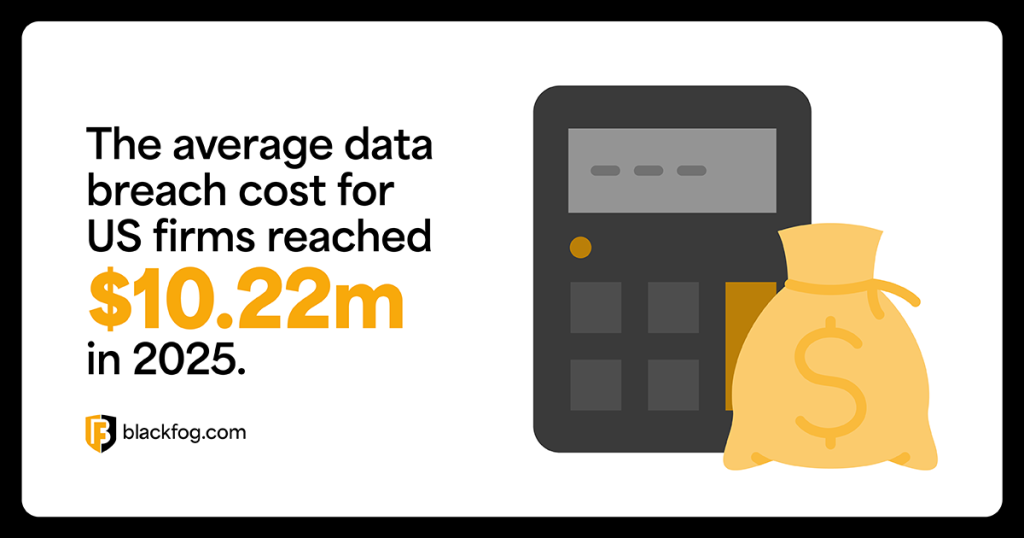
In addition to the legal consequences of a data breach, the financial challenges are also especially significant in the US. While figures from IBM show that global breach costs fell in 2025, the average cost for US companies actually rose by nine percent, hitting an all-time high of $10.22 million. The research highlighted higher regulatory fines and detection costs as key contributors to this.
The 7 Critical Phases Of A Data Breach Response Plan
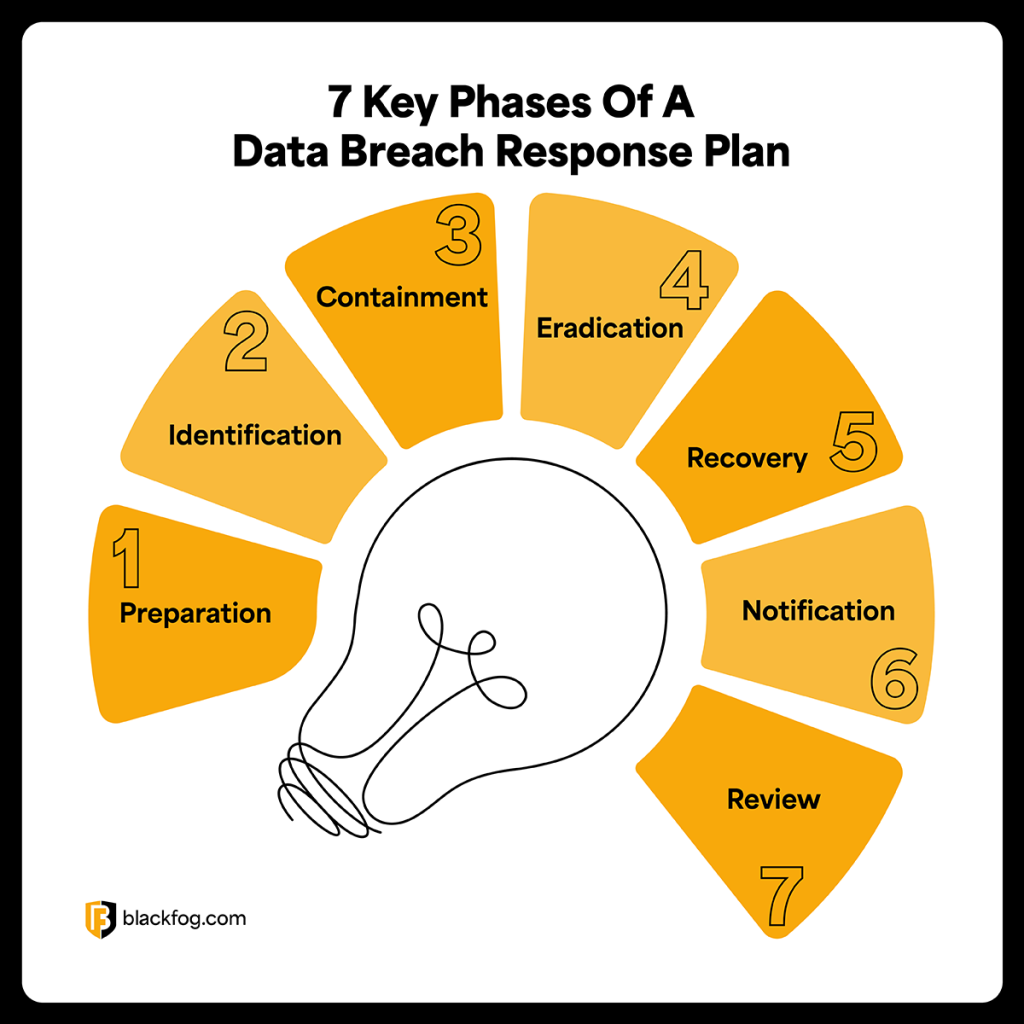
No two data breaches are identical. However, they will typically have common goals in mind, so most effective responses should follow a consistent structure. Having clearly defined phases ensures that nothing is overlooked in the chaos of an active incident, that responsibilities are assigned in advance and that the organization can move from detection to recovery in the most efficient and controlled way possible. The seven phases below form the foundation of a robust data breach response plan.
1. Preparation
Preparation happens before any incident occurs and is the foundation everything else depends on. This phase involves the entire organization, from the C-suite and legal counsel through to IT and communications teams. Key activities include:
- Assign a dedicated breach response team with clear ownership of the plan.
- Define roles and responsibilities so every team member knows their function during an incident.
- Establish communication protocols covering internal escalation and external disclosure.
- Draft notification templates for regulators, customers and partners.
- Conduct tabletop exercises to stress-test the plan before a real incident strikes.
2. Identification
Identification is the process of detecting that a breach has occurred or is in progress. Speed is a crucial factor in this, as the faster an intrusion is spotted, the greater the opportunity to limit its impact. This phase is primarily led by IT and security teams, supported by any managed security service providers the organization works with. Essential activities at this stage are:
- Deploy continuous monitoring tools to maintain real-time visibility across networks, endpoints and systems.
- Implement behavioral analysis to flag anomalous user activity that may indicate compromised credentials or insider threats.
- Monitor network traffic for unusual patterns such as unexpected data transfers or lateral movement between systems.
- Deploy anti data exfiltration tools to identify attempts to move sensitive information outside the organization’s environment.
- Establish clear alert thresholds so that potential incidents are escalated to the response team promptly while reducing the risk of false positives.
3. Containment
Once a breach has been identified, the first priority must be limiting the damage. Containment typically falls to IT and security teams, working under the direction of the response team lead. The key here is balancing the urgency of stopping the attack with the need to minimize downtime and preserve evidence for investigation and potential legal proceedings.
Steps taken during this phase include:
- Isolate affected systems by segmenting or taking offline any devices or networks showing signs of compromise.
- Block data exfiltration pathways by restricting outbound traffic and closing channels being used to remove data.
- Disable and remove compromised accounts to cut off threat actor access and prevent lateral movement.
- Preserve forensic evidence by capturing logs, memory dumps and network data before remediation begins.
4. Eradication
Eradication follows containment and focuses on removing the threat entirely from the organization’s environment. Led by IT and security teams, this phase ensures that no trace of the attack remains before systems are restored.
This phase should cover:
- Remove all malware and malicious code identified during the investigation, including any tools or scripts deployed by the attacker.
- Eliminate backdoors that threat actors may have installed to maintain persistent access to systems.
- Patch or remediate exploited vulnerabilities to close the specific weaknesses that enabled the breach.
- Conduct a thorough sweep of the entire environment to confirm no remnants of the intrusion remain.
5. Recovery
Effective recovery means the controlled restoration of systems and operations once security teams are certain the threat has been removed. The focus here is not simply getting back online quickly, but doing so safely. At this stage, organizations should:
- Restore systems from clean backups verified as predating the breach to avoid reintroducing compromised data.
- Validate system integrity before reconnecting anything to the wider network or resuming normal operations.
- Monitor restored systems closely in the immediate aftermath for any signs of recurring or residual malicious activity.
- Implement additional controls to address any weaknesses identified during the incident before bringing systems fully back online.
6. Notification And Legal Compliance
Notification must be handled carefully and promptly. Missteps here carry serious regulatory consequences and can significantly worsen reputational damage. Legal counsel should be closely involved throughout this phase alongside the communications and compliance teams. Obligations at this stage include:
- Determine reporting requirements by assessing which state, federal or industry regulations apply based on the data compromised and whose data is involved.
- Notify affected individuals clearly and promptly, providing details of what was compromised and what steps they should take.
- Report to relevant regulators within the timeframes mandated by applicable state and federal law.
- Communicate with stakeholders including partners, vendors and investors where contractual or legal obligations require it.
- Document all notification activity to demonstrate compliance in the event of regulatory scrutiny or litigation.
7. Post-Incident Review
The post-incident review is a key opportunity to strengthen the organization’s security posture and take positives from an incident. This phase should involve all stakeholders who played a role in the response, with its findings directly informing updates to the breach response plan itself. Organizations should ensure they:
- Conduct a full debrief with all response team members to document what happened, how it was handled and where gaps emerged.
- Identify root causes of the breach to ensure the underlying vulnerabilities are fully understood and addressed.
- Update the response plan to reflect lessons learned and close any procedural weaknesses the incident exposed.
- Strengthen defenses by implementing additional controls, employee training or security tools identified as necessary during the review.
- Schedule follow-up testing to validate that remediation measures have been effective and that the updated plan is fit for purpose.
Who Should Be On A Data Breach Response Team?
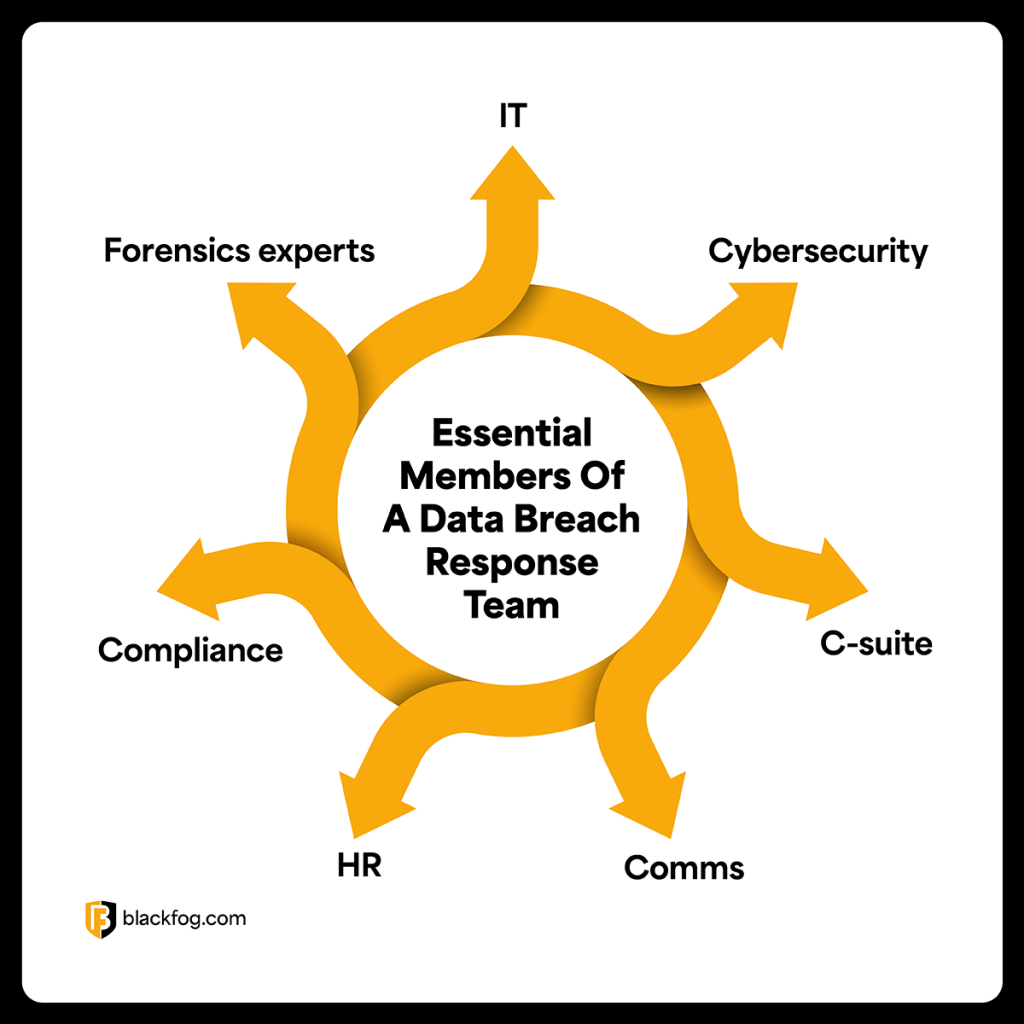
A data breach is not solely an IT problem. An effective response demands coordination across the entire business, with each function playing a defined role. Leaving incident management to security teams alone creates dangerous blind spots. Essential personnel include:
- IT and security leads: Manage technical containment, eradication and system recovery.
- Legal counsel: Navigate regulatory obligations, manage liability and oversee notification compliance.
- C-suite executives: Make high-stakes decisions quickly and provide organizational authority when needed.
- Communications and PR: Manage external messaging and protect reputation with customers and media.
- HR: Handle any insider threat dimensions and manage employee communications.
- Compliance officers: Ensure all actions align with applicable regulatory frameworks throughout the response.
- External forensic experts: Provide specialist investigation capabilities and independent validation of containment and eradication measures.
Good communication between all these departments is essential to success. To achieve this, breach response plans should set out clearly who is responsible for what elements of the plan and how they should maintain contact and provide updates throughout the process.
Common Mistakes That Worsen A Data Breach
How a business responds in the immediate aftermath of a breach can be just as consequential as the attack itself. Errors made under pressure can escalate regulatory penalties, expose the organization to class-action lawsuits and data breach compensation claims, and inflict reputational damage that persists long after the incident is resolved, or even collapse the entire business, as was the case in the 2025 NPD breach.
The most damaging mistakes include:
- Delayed detection: Failing to identify a breach early greatly increases both the volume of data compromised and the cost of recovery.
- Paying ransom without containment: Paying does not guarantee data recovery and leaves the underlying vulnerability unaddressed.
- Poor internal communication: Siloed responses create confusion, slow decision-making and increase the risk of regulatory missteps.
- Not preserving evidence: Compromising forensic data undermines investigation efforts and weakens the organization’s legal position.
- Failing to document response actions: Without clear records, demonstrating regulatory compliance becomes extremely difficult.
- Underestimating regulatory consequences: Many businesses focus on recovery while overlooking notification deadlines, increasing their legal exposure significantly.
A Data Breach Response Plan Checklist To Improve Performance
Getting a data breach response plan in place early – long before an incident occurs – gives businesses the best chance of minimizing damage. The following checklist is a practical framework to follow when building a solution.
Build your team
- Name a response team lead with clear authority.
- Document roles for all key personnel.
- Identify external forensic experts and legal counsel and have them on call.
Know your obligations
- Map and record all applicable state and federal reporting requirements.
- Pre-draft notification templates and have them ready to send.
Prioritize detection
- Deploy monitoring tools across all networks and endpoints.
- Define alert thresholds and escalation paths clearly.
Document containment plans
- Write down containment procedures and make them accessible to the whole team.
- Verify backups are clean, tested and up to date.
Protect evidence
- Establish evidence preservation protocols and communicate them to all team members.
- Log and timestamp all response actions during an incident.
Adapt and review
- Schedule tabletop exercises at least once a year.
- Review the plan after every incident or major organizational change.
No response plan eliminates risk entirely, but businesses that prepare thoroughly are significantly better positioned to contain damage, meet their legal obligations and maintain customer trust. This also ensures that when the time comes, no time is wasted wondering what to do – the answers are already there.
Data Breach Response Plan FAQs
What is the first step in a data breach response plan?
Preparation is the first step. This means assembling a response team, defining roles, establishing communication protocols and conducting practice exercises before any incident occurs.
How quickly must a business report a breach in the US?
It varies. A growing number of states mandate notification within 30 days, while sector-specific federal regulations such as HIPAA impose their own deadlines. Businesses must understand the requirements specific to their location and industry.
What is the difference between a security incident and a data breach?
A security incident covers events such as failed intrusion attempts or malware detections that don’t necessarily result in data access. A data breach is a specific incident where unauthorized parties have accessed or exfiltrated sensitive data, triggering legal notification obligations.
How can companies reduce financial exposure after a breach?
Speed is the most important factor. Faster detection and containment directly reduces costs. Having legal counsel involved from the outset also limits liability from regulatory fines and compensation claims.
Share This Story, Choose Your Platform!
Related Posts
Essential Lessons Businesses Should Learn From The NPD Breach
Learn what happened in the NPD breach, what data was exposed and the key lessons businesses should take to reduce the risk of a similar incident.
The Importance Of A Data Breach Response Plan: Essential Management Steps
What must businesses do to stand the best chance of recovering quickly from a cyberattack? This comprehensive guide covers key steps in any data breach response plan and how to implement them.
10 Data Exfiltration Risks That Emerge With Agentic AI
From poisoned tool descriptions to agent memory attacks, agentic AI creates data exfiltration pathways that traditional security controls cannot detect. Here are 10 threats to watch for and what you can do about them.
Agentic AI: The Data Exfiltration Risk Hiding Inside Your AI Agent
Agentic AI is creating unsupervised data exfiltration paths that traditional security tools struggle to detect. This blog examines the attack surface and how to address it.
From Zoom Calls to Desert Adventures: Our First Ever BlackFog Kick Off
BlackFog’s first global Kick Off brought the team together in Arizona for strategy, connection, and unforgettable desert adventures.
The Marks & Spencer Cyberattack One Year On
In April 2025, Marks & Spencer was hit by a major ransomware attack that exposed how modern cyber threats truly work. A year later, it stands as a clear example of the risks posed by data exfiltration, social engineering, and third-party compromise.