
Organized Cybercrime Groups
There are different categories of cybercriminals that can come together to form organized cybercrime groups. These include bored teenagers getting involved in petty online crimes, individual actors primarily motivated by financial gain, politically or ideologically motivated hackers, and fully fledged organized crime syndicates. However, the most sophisticated and damaging cybercrime operations tend to be carried out by the latter.
Successful organized cybercrime groups have a role-based structure where individual members contribute different specialized skills. One of the most common roles is that of the “penetration tester,” hackers who are particularly adept at gaining unauthorized access to computer systems and networks through vulnerabilities. Groups may have a single top-tier penetration tester or a team working in coordination.
Other core roles include technical experts who develop malware payloads or configure ransomware, negotiators who communicate with victims during extortion scenarios, money launderers skilled at obscuring illicit proceeds, and organizers who coordinate the overall criminal operation. This specialization allows groups to efficiently carry out complex multi-stage attacks.
Reputation is everything
Online forums devoted to talking about hacking and digital crime are the birthplace of many collaborations and upcoming formalized cybercrime organizations. By offering services or samples of their work, willing specialists will gradually create a name for themselves.
For example, a skilled penetration tester might share technical details and evidence of successfully compromised systems to advertise their abilities. Others demonstrate skills like malware authoring that are highly valued within the criminal community. Gradually, as reputations are earned, direct business relationships form between regular forum members needing certain services filled and these individuals.
Restricted Membership
Partnerships
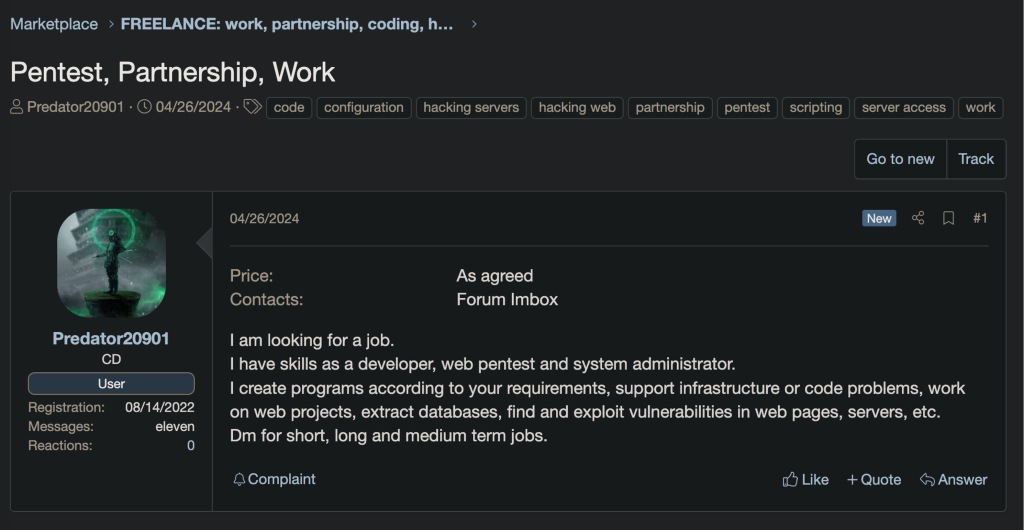
An example of a cybercriminal looking for a partnership
A notable example of the membership and ranking structure found on cybercrime forums can be observed in the Darkode archives leak. From 2007 to 2015, Darkode was an invite-only forum for cybercrime. It served as a platform for cybercriminals to exchange hacking techniques, buy and sell illegal goods and services, and work together on illegal schemes. Darkode was only accessible to invited members, and new users needed the endorsement of an existing user to be approved by administrators.

Darkode
An example of the membership system available on Darkode
After an administrator granted a user access to the forum, new members joined at level 0 or below, and they were frequently promoted from there after earning the trust of other members and offering helpful knowledge or skills.

Skillsets
An example of a cybercriminal offering a specific skillset
Ransomware Operations
One of the most visible and financially driven areas within organized cybercrime currently involves ransomware operations. Well-practiced cybercrime teams compromise systems, deploy ransomware payloads, and demand payments, often in cryptocurrency, in exchange for decryption keys.

Ransomware as a Service
Example of a RaaS affiliate program
The most formidable ransomware syndicates function like modern businesses with defined corporate structures, marketing, customer service protocols, and common diversification into extortion affiliate models.
Typical roles include programmers, distributors, negotiators, money launderers, and even “help desk” technicians. These hacking enterprises can generate hundreds of millions annually from worldwide victims and have grown into transnational networks that span continents.
Frequently Asked Questions
Below are some common questions people have about the formation and operations of organized cybercrime groups:
Prevent Cybercrime with BlackFog ADX
BlackFog provides a solution with a focus on preventing data exfiltration with ADX technology. This next generation cybersecurity solution has been designed to help organizations protect themselves from ransomware attacks and extortion 24/7, without the need for human intervention.
Don’t wait for the next ransomware attack wave; take proactive action now and secure your most valuable asset.
Learn how our solutions can strengthen your cybersecurity posture and prevent ransomware incidents.
Share This Story, Choose Your Platform!
Related Posts
LotAI: How Attackers Weaponize AI Assistants for Data Exfiltration
What happens when attackers use your approved AI tools as a data exfiltration channel? New research reveals how the LotAI technique turns Copilot and Grok into covert C2 relays.
The State of Ransomware: February 2026
BlackFog's state of ransomware February 2026 measures publicly disclosed and non-disclosed attacks globally.
Steaelite RAT Enables Double Extortion Attacks from a Single Panel
Steaelite is a newly emerging RAT that unifies credential theft, data exfiltration, and ransomware in a single web panel, accelerating double extortion attacks.
ClawdBot and OpenClaw: When Local AI Becomes A Data Exfiltration Goldmine
ClawdBot stores API keys, chat histories, and user memories in plaintext files, and infostealers like RedLine, Lumma, and Vidar are already targeting it.
West Harlem Group Assistance Stops Ransomware and Cryptojacking with BlackFog ADX
West Harlem Group Assistance secures its community mission by preventing ransomware and cryptojacking with BlackFog ADX.
Why Traditional Security Fails To Deal With Advanced Persistent Threats
Learn why advanced persistent threats remain a growing cybersecurity risk in 2026 and where organizations must focus to address them.






