
Ransomware in energy and utilities, such as attacks on energy, oil and gas have become more frequent, more disruptive, and more costly.
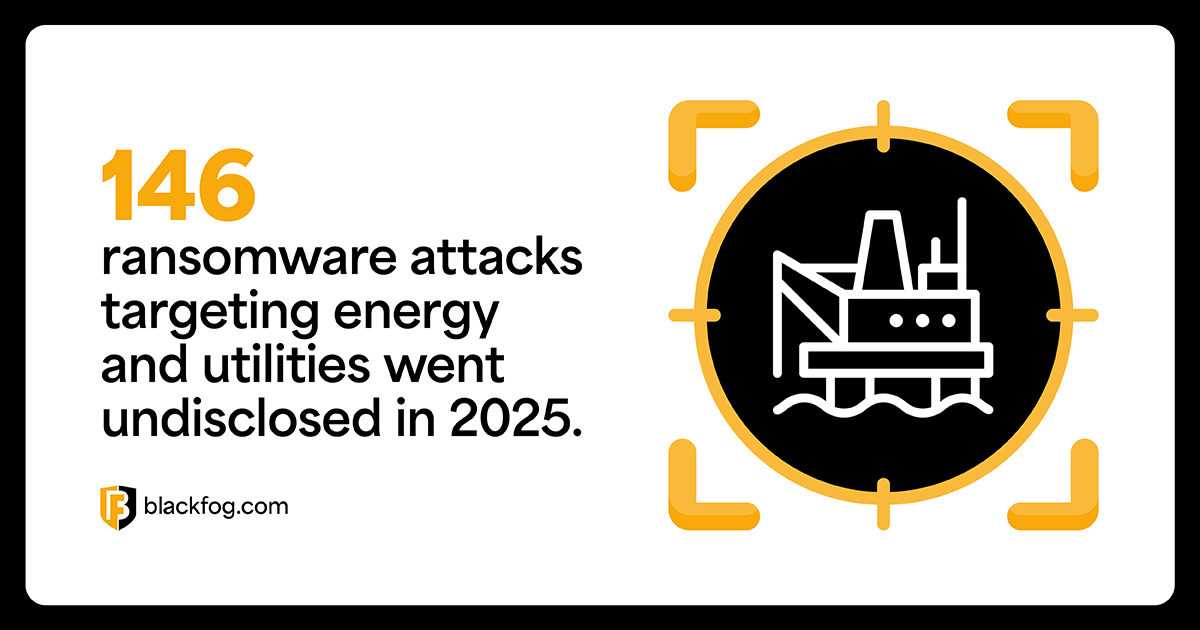
These are no longer isolated IT incidents. They are disrupting operations, exposing sensitive infrastructure data, and costing organizations millions. What is visible publicly, however, is only part of the picture. In 2025 alone, 146 ransomware attacks targeting energy and utilities went undisclosed, highlighting how much activity remains out of sight.
The Attacks Shaping the Sector
Halliburton (US) Data Theft and Operational Disruption at Scale
Group: Linked to the RansomHub
In mid-2024, Halliburton disclosed that an unauthorized third-party had gained access to its systems, forcing the company to take parts of its IT infrastructure offline.
The impact was immediate. Internal systems were shut down to contain the attack, customers were disconnected from services, and core business functions including invoicing and procurement were disrupted.
Attackers also exfiltrated data from the network, combining disruption with extortion. The company later reported approximately $35 million in losses, underlining how quickly a cyber incident can translate into material financial damage.
This was not a contained incident. It affected a company embedded across global energy supply chains.
American Water (US) Disruption at the Largest Public Utility
American Water, the largest publicly traded water utility in the United States, was hit by a cyberattack that forced the company to shut down parts of its IT systems to contain the incident.
Customer-facing services, including billing and online portals, were taken offline as a precaution. While water and wastewater operations continued, the disruption affected services for millions of customers.
This incident highlights how attacks on IT systems alone can still have widespread impact across critical infrastructure, even when core operations remain unaffected.
Romanian National Water Agency Critical Infrastructure at Scale
A ransomware attack on Romania’s national water authority, Administrația Națională Apele Române (ANAR), highlighted the growing risk to public utilities.
The attack compromised around 1,000 systems, including core IT infrastructure such as servers, databases, and internal platforms, and spread across multiple regional water administrations. Attackers used built-in tools like BitLocker to encrypt systems, forcing parts of the organization offline.
While water operations continued, the agency had to rely on manual processes after losing visibility across key systems.
The incident was not isolated. Around the same period, Romanian oil pipeline operator Conpet was also targeted in a ransomware attack, forcing the company to isolate affected systems and activate incident response measures while maintaining operations.
Together, these incidents highlight how ransomware is increasingly targeting both utilities and energy transport infrastructure, disrupting IT systems while forcing organizations into manual, degraded modes of operation.
Pakistan Petroleum Limited A Near Miss for Operational Technology
Group: Blue Locker
Pakistan’s oil and gas sector came under direct ransomware pressure in 2025, with Pakistan Petroleum Limited (PPL) among the confirmed victims of the Blue Locker campaign.
Attackers gained access to internal systems, encrypted servers, and disrupted operations, prompting warnings to critical infrastructure organizations.
While the intrusion impacted IT systems, core production systems remained unaffected due to containment measures.
This incident highlights how ransomware campaigns are actively targeting national energy infrastructure and how quickly disruption can escalate without effective controls.
Why Energy and Utilities Are Being Targeted
These attacks are not random. Energy and utilities providers present a combination of factors that make them ideal targets.
Immediate Operational Impact
When systems are disrupted, production can stop, services are interrupted, and revenue is affected. This creates urgency, and urgency increases the likelihood of payment.
High-Value Data
Energy providers hold sensitive data including infrastructure designs, operational systems, and supply chain dependencies.
In incidents like Halliburton, data was exfiltrated alongside system disruption. That data can then be used for extortion, resale, or future attacks.
Complex Environments
Energy and utilities providers operate across legacy systems, IT and operational technology environments, and large distributed networks.
These environments increase the attack surface and make it more difficult to detect and prevent data exfiltration.
The Attacks You Don’t See
Despite the severity of the incidents outlined above, they represent only part of the threat landscape.
The 146 undisclosed attacks in 2025 point to a consistent pattern. Many incidents are contained before disruption, others focus solely on data exfiltration, and some are never reported publicly.
This reflects a fundamental shift.
Ransomware is no longer defined by encryption alone. It is defined by the ability to access and exfiltrate data, often without immediate visibility.
Ransomware in energy and utilities sector is becoming more targeted and more effective.
The attacks highlighted here show how disruption, data theft, and operational pressure are being used together to maximize impact. At the same time, the increasing number of undisclosed ransomware incidents demonstrate how much of this activity happens without visibility.
This is the shift. Ransomware is no longer defined by systems being locked. It is defined by data being taken.
The organizations that stay ahead of ransomware and extortion will be those that focus on preventing data exfiltration at the source before attackers can monetize it.
BlackFog’s ADX platform uses AI based anti data exfiltration technology to block ransomware at the source, preventing unauthorized data from ever leaving your endpoints. Rather than relying on detection after a breach occurs, ADX proactively monitors and blocks suspicious outbound traffic in real time, neutralizing threats like Interlock before they can extract sensitive patient data.
Learn more here: ADX Protect.
Share This Story, Choose Your Platform!
Related Posts
The State of Ransomware: April 2026
BlackFog's state of ransomware April 2026 measures publicly disclosed and non-disclosed attacks globally.
BlackFog Q1 2026 Ransomware Report: Only 1 in 9 Ransomware Attacks Made Public as Data Exfiltration Hits 96%
BlackFog Q1 2026 Ransomware Report reveals only 1 in 9 attacks are disclosed as data exfiltration hits 96% worldwide.
2026 Q1 Ransomware Report
BlackFog’s 2026 Q1 Ransomware Report - Ransomware Remains Relentless with Data Exfiltration Holding at 96%
Shadow AI and Governance: Why Traditional Control Is Failing CISOs
Shadow AI and Governance: Why traditional controls are failing CISOs as AI adoption accelerates, increasing risk and reducing visibility.
Ransomware in Energy and Utilities: The Real Story Behind the Attacks
Ransomware in energy and utilities is rising, combining disruption, data theft, and extortion across critical infrastructure.
Oracle Breach: What Happened and Why It Matters
The 2025 Oracle breach exposed millions of records across three separate incidents. Learn how attackers got in, which industries were hit, and how to protect your organization.





