
Why do Businesses Need Advanced Enterprise DLP Solutions?
Data loss is one of the biggest cyberthreats faced by any large enterprise. Such firms now manage vast amounts of information and filing to keep this safe can lead to a wide range of consequences. These can include confidential data ending up in the hands of competitors or criminals who demand a ransom for the return or deletion of data. Beyond them, data protection failings also expose enterprises to severe regulatory penalties or reputational damage.
Therefore, a specialized enterprise-grade data loss prevention tool, or DLP, needs to play a role in every cybersecurity solution. These work differently to traditional defenses such as firewalls and anti-malware as they focus on what’s leaving the enterprise, not what’s entering it.
These technologies play a key role in data breach prevention by stopping incidents before they have a chance to damage your business.
What is Data Loss Prevention?
Data loss prevention is a wide-ranging area that covers much more than just cyberthreats. It includes all the tools, technologies and processes needed to protect data from accidental deletion, loss or theft. Done right, it prevents unauthorized sharing of sensitive data and protects firms from threats such as ransomware and extortion.
While basic DLP tools typically rely on simple rules to flag or block obvious data leaks, such as keyword matching or file transfer monitoring, enterprise-grade DLP goes much further. This is designed for large and distributed environments where data moves across endpoints, cloud platforms and third-party services. It uses contextual analysis to understand who is accessing data, how it is being used and whether that activity aligns with data loss prevention policies. This allows organizations to enforce precise controls, reduce false positives and protect sensitive data at scale.
Tackling the Modern Challenges of Data Protection
Guarding against accidental or malicious data loss should be a key part of any firm’s data protection strategy, especially in an evolving environment where data sprawl and the growth of cloud solutions, hybrid work and unmanaged endpoints create more opportunities for data loss.
On top of this, one of the biggest data security issues facing many firms today is that hackers will often be specifically targeting data and traditional DLP solutions may struggle to keep up with such a complex landscape. Advanced techniques like DNS exfiltration make data theft harder to detect – and once information has left the enterprise, it’s too late. In such cases, firms will feel they have no choice but to give in to whatever hackers demand in order to restore access or prevent the public disclosure of sensitive information.
The Risks Posed by Data Loss
The main risks posed by a data leak can broadly be broken down into three categories: financial, reputational and operational. Each of these can be hugely expensive and, when taken together, the overall cost of a data loss incident can easily run into the millions of dollars.
- Financial: This covers any direct costs caused by data loss. It may include compensation or class-action settlements for affected users, fines from data protection regulators and the cost of restoring and hardening systems. It also includes any direct ransoms paid to hackers in order to recover data.
- Operational: Any data loss that prevents firms from conducting day-to-day business can also be expensive. Research by the Uptime Institute indicates more than half of businesses say their most recent downtime cost more than $100,000, while in some cases, such as the 2025 Jaguar Land Rover ransomware incident, critical operations can be disrupted for weeks or even months.
- Reputational: Perhaps the farthest-reaching, yet hardest to quantify loss comes from any reputational damage. This is especially the case if customers have had highly sensitive information stolen. According to ISACA, one in three consumers have cut ties with a company because of a data breach.
What Techniques are Commonly Used for DLP?
Traditional network DLP tools use a variety of technologies to stop any data leakage issues as they occur. Typically, such solutions rely on tried and tested methods such as signature matching and file tagging tools to spot data breaches. These usually work in parallel with other solutions such as firewalls, email security and intrusion detection systems to guard against external threats.
However, more advanced endpoint protection can go far beyond this. By using a behavioral-based approach, an anti data exfiltration and DLP solution can work together to quickly spot unusual activity that may indicate data breaches in progress, and shut it down before hackers have the chance to remove confidential information from the network.
Why do Organizations Need Modern Data Loss Prevention Solutions?
The tactics used by hackers are changing all the time, so traditional enterprise DLP tools alone may not be enough. Common problems include an inability to discriminate between users, which makes it hard for these systems to identify whether an issue is the result of carelessness, a malicious insider threat or an external data breach attempt.
Legacy tools are also very resource-intensive and come with high costs and maintenance requirements. This can make them impractical for small firms or those with limited IT teams. Therefore, more modern anti data exfiltration solutions that address these drawbacks must be considered in order to extend the protection DLP tools offer.
Key Considerations For Enterprise Data Loss Prevention Programs
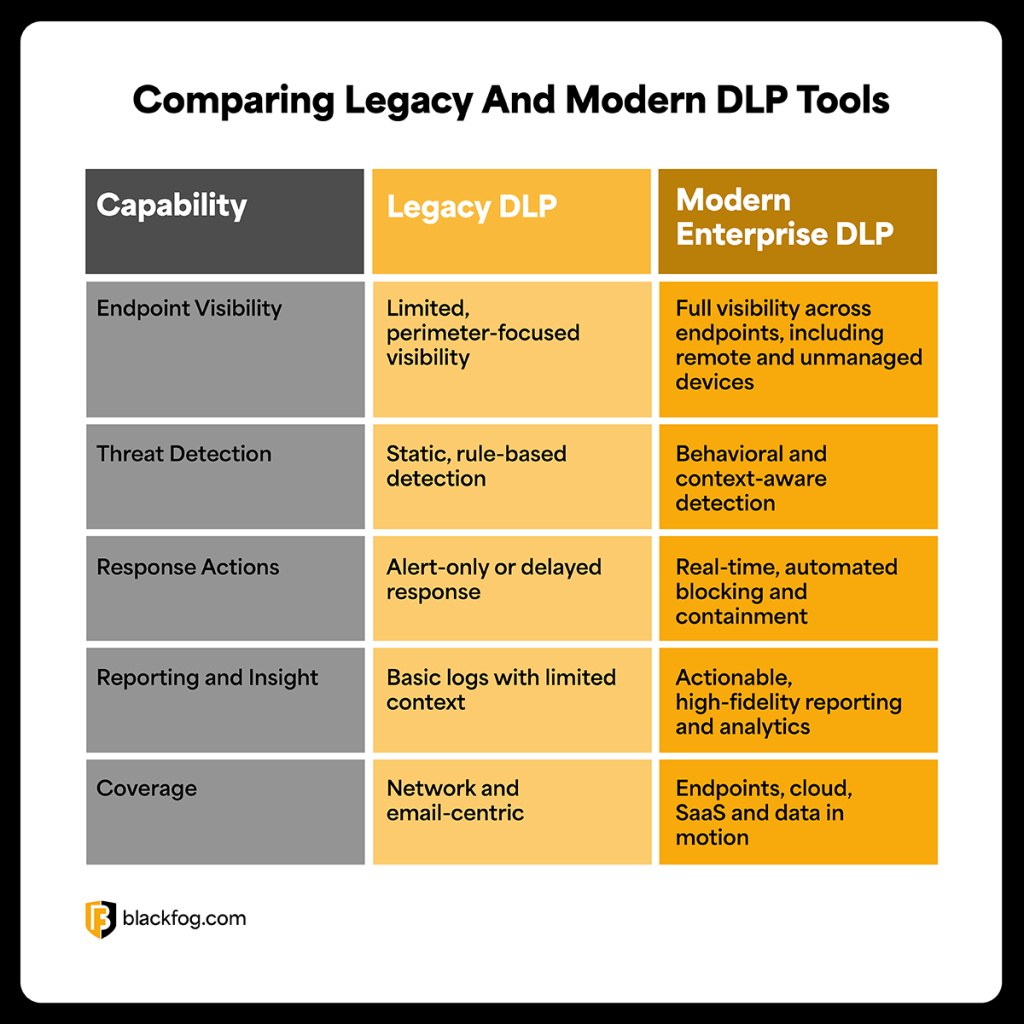
Building an effective data loss prevention strategy requires more than deploying basic controls or relying on legacy tools designed for simpler environments. As data now moves constantly across endpoints, cloud platforms and remote workforces, enterprises must evaluate whether their DLP capabilities can provide the visibility, detection and response needed to prevent modern data exfiltration threats. The comparison below highlights the key differences between traditional DLP approaches and modern, enterprise-grade solutions, and the factors organizations should consider when protecting sensitive data at scale.
Integrated DLP vs. Enterprise Data Loss Prevention
When evaluating data protection solutions, enterprises will often encounter two terms used to describe DLP capabilities: integrated DLP and enterprise data loss prevention. While they sound similar, they refer to very different approaches to protecting sensitive data.
Integrated DLP describes basic, built-in controls that are often offered as part of a wider platform, such as email tools, cloud storage or endpoint security products. These solutions tend to be siloed and rely on static rules with limited context.
True enterprise data loss prevention, however, is a dedicated solution that applies a unified policy across endpoints, networks and cloud environments. By analyzing data sensitivity and user behavior in real-time, it enables more accurate enforcement, reduces false positives and allows organizations to stop exfiltration of data without disrupting legitimate business activity.
What are the Benefits of Deploying an Endpoint DLP?
To stand the best chance of defending against data theft, enterprises need to look beyond network-level DLP tools and ensure security at the device layer. To effectively protect every endpoint against data loss, dedicated anti data exfiltration tools offer the next evolution in endpoint protection.
By analyzing activity on every device, these solutions can build up a complete, accurate picture of what normal data transfers look like. Then, set up DLP rules detailing how to respond, letting the technology step in automatically to block any suspicious behavior that could be a hallmark of a data exfiltration attempt.
Share This Story, Choose Your Platform!
Related Posts
ClawdBot and OpenClaw: When Local AI Becomes A Data Exfiltration Goldmine
ClawdBot stores API keys, chat histories, and user memories in plaintext files, and infostealers like RedLine, Lumma, and Vidar are already targeting it.
West Harlem Group Assistance Stops Ransomware and Cryptojacking with BlackFog ADX
West Harlem Group Assistance secures its community mission by preventing ransomware and cryptojacking with BlackFog ADX.
Why Traditional Security Fails To Deal With Advanced Persistent Threats
Learn why advanced persistent threats remain a growing cybersecurity risk in 2026 and where organizations must focus to address them.
What Does Advanced Threat Protection Really Mean In 2026?
Find out why businesses need advanced threat protection to cope with the new era of sophisticated, persistent cyber risks.
How Can You Prevent Viruses And Malicious Code Today?
Preventing viruses and malicious code is harder than ever in a landscape where APTs are a growing threat. Here's what you need to know to stay safe.
Security Vulnerabilities That Enable Persistent Cyber Threats
Understanding the most common security vulnerabilities that enable advanced persistent threats is critical to protecting businesses in 2026.






