
Understanding Ransomware Decryptors and How They Can Be Used
When it comes to malware and ransomware, prevention is always the best defense. Strong cybersecurity measures, regular backups and user awareness are critical to avoiding costly breaches. However, even the most prepared businesses can sometimes fall victim to sophisticated attacks.
If defenses are breached and critical data is encrypted, having safe, reliable recovery options becomes essential. This is where ransomware decryptors can play a key role. In certain cases, these tools offer a way to unlock encrypted files without paying a ransom, helping organizations recover quickly and avoid further financial or reputational harm.
What Is a Ransomware Decryptor and How Does It Work?
A ransomware decryptor is a specialized tool designed to help businesses recover encrypted files without having to hand money to attackers for decryption keys. These tools work by exploiting weaknesses in the encryption methods used by specific strains of ransomware, or by using decryption keys that have already been seized by law enforcement.
For instance, last year, the FBI secured over 7,000 LockBit ransomware keys that victims could use to recover files. However, there are also a range of free and commercial tools that can be used.
Decryptors can be a vital recovery option when firm have failed to detect ransomware early enough and backups are unavailable, incomplete or compromised during an attack. However, decryptors are not universal solutions – they are only effective against certain ransomware variants where flaws or key leaks have already been identified.
How Ransomware Decryptors Work
When a ransomware attack encrypts files, it uses a cryptographic algorithm to scramble the data. If researchers can reverse-engineer the encryption method, find mistakes in how the ransomware was coded, or obtain the private decryption key, they can build a decryptor tool. This is then used to safely restore access to the affected files without needing to negotiate with the attackers or pay a ransom. In order to work effectively, decryptors must be matched precisely to the ransomware strain involved.
When Can Firms Use a Ransomware Decryptor?
Ransomware decryptors can be a valuable tool when key business data has been encrypted and no clean backups are available. However, decryptors are only effective against certain ransomware families, typically older or less sophisticated strains where weaknesses in the encryption have been discovered. Not every ransomware attack will have a decryptor solution available, especially with newer or more advanced variants.
Before attempting to use a decryptor, it is essential to correctly identify the specific type of ransomware involved. Using the wrong decryptor can cause further data damage or make recovery impossible. Using ransomware identification tools is a key step in this. Once identified, businesses can search trusted sources to find a legitimate decryptor if one exists. Accurate identification is the first and most critical step in safe recovery.
The Importance of Using Trusted Decryptors
While ransomware decryptors can be highly effective, businesses must exercise extreme caution when searching for these tools. Downloading a decryptor from an unverified or suspicious source can lead to further compromise, including the installation of additional malware, theft of sensitive information or permanent corruption of encrypted files.
Attackers sometimes disguise their own malware as fake decryptor tools to exploit desperate victims. To stay safe, firms should only download decryptors from reputable cybersecurity organizations, government initiatives like Europol’s No More Ransom initiative, or trusted cybersecurity vendors. Using only verified sources is essential to avoid making a bad situation even worse.
Limitations of Ransomware Decryptors
While ransomware decryptors can be a valuable recovery tool, businesses cannot rely on them as a guaranteed solution, especially against newer, more sophisticated ransomware variants. Relying on them as a standalone solution carries several limitations, including:
- Ineffective against modern threats: Many newer ransomware strains use advanced encryption and double extortion tactics – exfiltrating sensitive data before locking systems -making decryptors insufficient.
- Data exfiltration remains an issue: The majority of ransomware attacks now aim to steal data before encryption. Even if a decryptor successfully restores access to encrypted files, it cannot undo the damage of stolen or leaked information.
- The need for technical expertise: >Using a decryptor improperly can corrupt data further and leave systems open to reinfection. Some firms may not have the technical know-how to avoid such issues.
Ultimately, the most reliable defense against ransomware remains maintaining strong, secure and regularly tested backups. A clean, isolated backup allows businesses to restore operations quickly and safely without depending on decryptors or negotiating with attackers.
Should You Pay the Ransom?
When faced with a ransomware attack and no available decryptor, some businesses may consider paying the ransom in the hope of recovering their data quickly. The pressure to resume operations and avoid reputational harm can be intense. However, best practice from cybersecurity experts and law enforcement agencies is clear: do not pay the ransom unless absolutely unavoidable.
Key reasons why paying is strongly discouraged include:
- No guarantee of data recovery: Attackers may not provide working decryption keys or may demand additional payments.
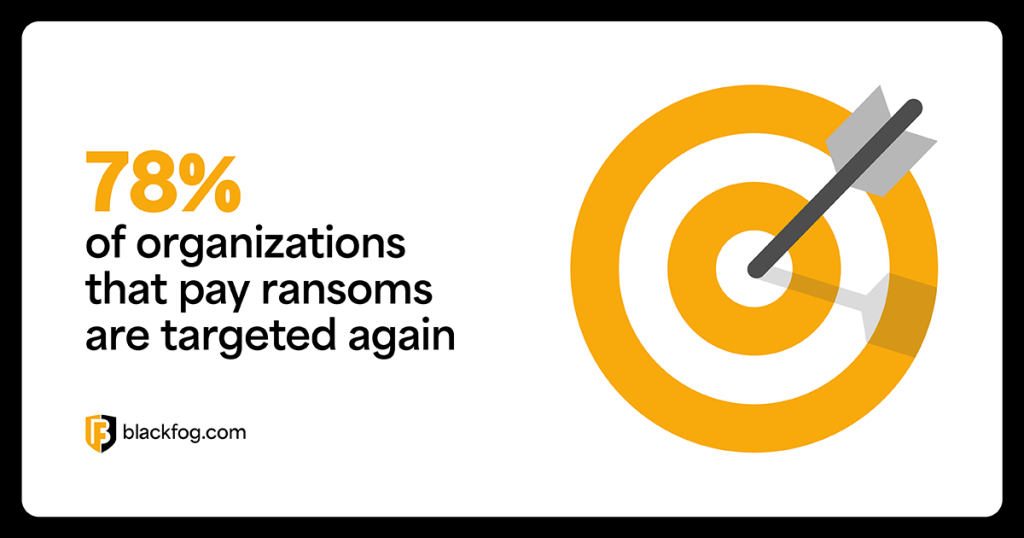
- Encouraging future attacks: Paying ransoms funds criminal activity and increases the likelihood of being targeted again. Indeed, one study by Cybereason found 78 percent of organizations that pay are targeted again.
- Potential legal and regulatory issues: In some jurisdictions, paying certain ransomware groups may breach sanctions laws, leading to legal penalties.
- Ongoing risk: Even after payment, attackers may retain stolen data, exposing businesses to future extortion.
Ultimately, prevention remains the strongest defense. In an environment where sophisticated double extortion ransomware is now the dominant method used by hackers, strong cybersecurity practices, robust backup strategies and early detection are critical to reducing risk and avoiding damage after an attack.
Share This Story, Choose Your Platform!
Related Posts
Steaelite RAT Enables Double Extortion Attacks from a Single Panel
Steaelite is a newly emerging RAT that unifies credential theft, data exfiltration, and ransomware in a single web panel, accelerating double extortion attacks.
ClawdBot and OpenClaw: When Local AI Becomes A Data Exfiltration Goldmine
ClawdBot stores API keys, chat histories, and user memories in plaintext files, and infostealers like RedLine, Lumma, and Vidar are already targeting it.
West Harlem Group Assistance Stops Ransomware and Cryptojacking with BlackFog ADX
West Harlem Group Assistance secures its community mission by preventing ransomware and cryptojacking with BlackFog ADX.
Why Traditional Security Fails To Deal With Advanced Persistent Threats
Learn why advanced persistent threats remain a growing cybersecurity risk in 2026 and where organizations must focus to address them.
What Does Advanced Threat Protection Really Mean In 2026?
Find out why businesses need advanced threat protection to cope with the new era of sophisticated, persistent cyber risks.
How Can You Prevent Viruses And Malicious Code Today?
Preventing viruses and malicious code is harder than ever in a landscape where APTs are a growing threat. Here's what you need to know to stay safe.






