
Effective Data Security Management: Strategies and Best Practices
Cybersecurity threat management is one of the biggest issues for any organization today. But while there are many aspects to this, one of the biggest focuses for every firm if they are to improve their cyber resiliency must be securing sensitive data from loss, theft or corruption.
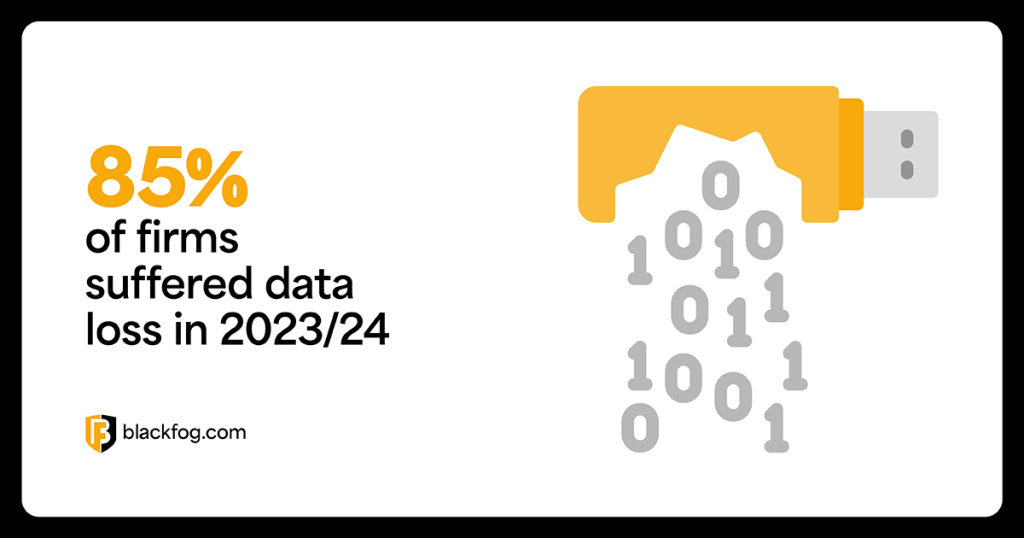
This matters because data loss of some kind is almost inevitable. Indeed, according to a 2024 study by Proofpoint, 85 percent of organizations experienced this in the past year, with 71 percent of businesses saying human error or carelessness was a major factor. Although accidental data loss remains a major issue, the growing threat of cybercrime and ransomware must also be addressed.
A common model for data security management is what’s known as the CIA triad. This stands for confidentiality, integrity and availability and means making sure data is only accessible to authorized personnel, is fully accurate and trustworthy and is on hand whenever it is needed.
Balancing accessibility with security is a major challenge – but getting it right is critical if firms are to stay safe without compromising their essential activities.
Understanding Data Security Management
Data security management is a broad term that covers all the operations firms must undertake to protect their most sensitive digital information from threats. There are many issues that can cause data to be lost, compromised or otherwise corrupted, including:
- External hacking attacks
- Careless or negligent employee behavior
- Malicious insiders
- Loss or theft of devices
- Hardware failure
- Natural disasters
A comprehensive management strategy is required to protect against these issues. This should focus on several aspects, including what tools and technologies will be used to defend against threats, the roles and responsibilities of everyone in the business – not just IT and security teams – and what steps need to be taken to recover in the event of a data breach.
It also needs to protect information across the entire data lifecycle, from creation and processing through to storage, archiving and eventually deletion. Good data security management policies should have clear sections for data retention, emphasizing that assets should only be kept when strictly necessary.
Why Data Security Management is Crucial
The loss of critical data – whether accidental or as a result of malicious activity – leads to a wide range of problems.
According to IBM, the average cost of a data breach in 2025 is $4.4 million. However, this has actually fallen by nine percent compared with the previous year, which the company noted illustrates the effectiveness of improved threat identification and containment measures.
Despite this, highly sensitive information remains particularly enticing to hackers.
These groups understand the damage that data loss can do to a business and have sought to exploit this through tactics such as double extortion ransomware.
By stealing data and then holding it hostage – often threatening to release it publicly unless they receive a payment – these criminals increase their chances of making money. Many businesses feel giving in will be cheaper and less disruptive, as well as avoiding any potential reputational damage.
A comprehensive data security management plan addresses this by ensuring that even if first lines of defense are breached, information cannot be exfiltrated from an organization.
Best Practices for Effective Data Security Management
A good data security posture management strategy needs to include a wide range of tools, technologies and policies in order to defend against these threats. Among the key components of this are the following activities:
- Data discovery and classification: This is essential in helping firms understand exactly what digital assets they possess, where these are located and which should receive the highest priority for security measures.
- Data governance: This covers all critical data handling and management policies related to how data is stored, accessed and processed. It’s vital in ensuring data privacy and security while still making mission-critical data available when needed.
- Backups: Ensuring all critical data is backed up in secondary locations, apart from the main network, can help mitigate downtime in the event of a data loss incident or ransomware attack that encrypts key files. As part of this, there should also be a clear plan for recovery.
- Access management: Controlling who has access to data and how they do this involves a range of steps. This includes enforcing strong password policies and multi-factor authentication to reduce the risks posed by stolen credentials, as well as monitoring tools to alert security teams to any suspicious activity.
- Employee training and culture: Human error is a leading cause of data breaches, so it’s essential everyone is aware of the importance of security and what their own responsibilities are. It’s important that security is deeply embedded in the company culture. This ranges from not sharing passwords or accessing data via unsecured Wi-Fi networks to undergoing training to help spot and report phishing attacks that may be an entry point for malware like infostealers.
- Incident response and recovery: Should a data breach occur, a clear plan for what to do is vital. This must include details on who is responsible for what activities, how backups and contingencies should be initiated and who needs to be informed, such as stakeholders and regulators.
It pays to have a clear security framework in place to help guide these activities. Options such as ISO 27001 or CIS Controls may help give businesses the direction they need.
What are the Different Types of Data Security?
There are a wide range of methods and techniques businesses can employ in order to achieve strong data protection. Among the most important are the following:
- Data encryption: This ensures that even if data is compromised, it will be unreadable by anyone without proper authorization and access to the right keys.
- Access control and authentication: Ensuring only an authorized user can view and edit sensitive data prevents hackers from moving laterally within a business, making it vital for both security and privacy.
- Email security: This channel remains the most common way for cybercriminals to access networks, so strong protection to guard against issues like phishing is crucial.
- Firewalls: An essential first line of defense in your network security, firewalls play a key role in preventing hackers from entering your network in the first place.
- Data masking: Especially important when dealing with personally identifiable information, steps to anonymize critical information or decouple it from specific individuals are hugely useful.
- Data erasure: While usually more of a data privacy concern, holding on to data beyond its useful life gives hackers more options to target, so you need a clear plan for deleting data once it’s served its purpose.
- Anti data exfiltration (ADX): A critical last line of defense, ADX solutions ensure that even if criminals do breach your network perimeter, they will be unable to remove data from the business.
Common Challenges and Solutions in Data Security Management
Developing a cybersecurity risk management solution is no easy task. Big data security will require firms to cover a huge amount of ground, while at the same time battling against constantly evolving cyberthreat attack strategies that are always looking for new weaknesses to exploit.
Here are some of the biggest challenges that businesses will have to tackle and how to deal with them:
New attack methods
Cybercriminals continually evolve their tactics, using fileless malware, AI-driven phishing, data poisoning of business AI tools and adaptive malware to evade detection. This means traditional defenses such as signature matching can no longer keep pace, leaving businesses exposed to threats that exploit legitimate tools or mimic trusted communications. AI adds another layer of complexity by enabling attackers to generate realistic phishing messages, deepfakes and adaptive malware that learns to bypass protections.
Solutions for this include:
- Implementing behavior-based threat detection.
- Investing in AI-driven defense tools to counter AI-enabled threats.
- Running regular phishing simulations to prepare employees for advanced social engineering.
Data sprawl
The rapid adoption of cloud computing and mobile devices has expanded the data landscape, often outside the visibility of IT teams. Sensitive information now moves between multiple cloud platforms, third-party services and unsecured personal devices. This dispersal increases the risk of data leakage and makes it difficult to apply consistent security controls.
Tackle this issue with the following steps:
- Conduct regular audits to map where data resides across the business.
- Use data loss prevention (DLP) tools to monitor data in motion and at rest.
- Use ADX technology to actively prevent unauthorized data exfiltration at the endpoint.
- Require encryption for data in transit and at rest to protect sensitive assets.
Evolving working patterns
Hybrid and remote work have pushed sensitive data beyond traditional network perimeters, with employees often connecting from unsecured devices and public Wi-Fi. This shift creates more attack entry points and raises the likelihood of compromised access through poorly protected endpoints or shadow IT.
These challenges can be met by:
- Implementing a zero trust security model where every device and user must be verified.
- Requiring VPN or secure access gateways for all remote connections.
- Enforcing endpoint protection policies and ADX use across BYOD and mobile devices.
The human factor
Human error remains the leading cause of breaches, whether through falling for phishing, misconfiguring systems, or mishandling sensitive data. Beyond mistakes, malicious insiders also pose risks, with insider-driven incidents often costing companies hundreds of thousands of dollars per attack. This dual risk makes people the most unpredictable part of any security strategy.
Reduce the risks of employee-driven data breaches by:
- Delivering ongoing, role-specific security awareness training with real-world simulations.
- Monitoring for anomalous behavior using behavioral analytics to flag insider threats early.
- Establishing clear reporting channels for suspicious activity and rewarding proactive employee vigilance.
Tools and Technologies for Data Security Management
Effective data security requires a defense-in-depth approach. No single tool can protect against every threat, so businesses need a layered strategy that combines perimeter defenses, continuous monitoring and endpoint safeguards to detect, contain and prevent attacks. Adopting zero trust principles is also essential, ensuring every user and device must prove legitimacy before gaining access. Key tools and technologies include:
- Next-generation firewalls, antimalware and email security: Block malicious traffic and phishing attempts at the perimeter before attackers enter the network.
- Security Information and Event Management (SIEM): Provide centralized monitoring and real-time alerts for suspicious activity, helping detect lateral movement once perimeter defenses are breached.
- Data Security Posture Management (DSPM): Continuously assess where sensitive data resides across cloud and hybrid environments, ensuring visibility and compliance with evolving regulations.
- Zero trust security models: Enforce strict identity verification, least privilege access and continuous authentication for all users and devices.
- ADX: Protect endpoints by preventing unauthorized data transfers in real-time, stopping both external hackers and malicious insiders from exfiltrating valuable information.
- Encryption and backup solutions: Keep sensitive data secure in transit and at rest, while ensuring recovery is possible in the event of an incident.
Share This Story, Choose Your Platform!
Related Posts
The State of Ransomware: March 2026
BlackFog's state of ransomware March 2026 measures publicly disclosed and non-disclosed attacks globally.
Venom Stealer Turns ClickFix Into a Full Exfiltration Pipeline
BlackFog analyzes Venom Stealer, a new MaaS infostealer that uses ClickFix delivery to launch an automated exfiltration pipeline covering credential theft, wallet cracking, and fund sweeping.
What Enterprises Need To Know About Cyber Governance, Risk And Compliance
Learn all about cyber governance, risk and compliance in 2026 and why this must be a consideration at the highest levels of all organizations.
Navigating Essential Cybersecurity Compliance Standards: What To Know
There are a range of cybersecurity compliance standards firms of all sizes must deal with, including mandatory and voluntary frameworks. Here's what you need to know.
Understanding The Requirements Of Information Security Compliance
Learn precisely what information security compliance entails and the various steps that go into making this effective.
The Importance Of Effective Cybersecurity Services For Small Businesses
Find out why cybersecurity services for small businesses are more in-demand than ever as cybercriminals shift their focus to less-sizable enterprises.






